|
[1]
|
李韬, 孟杨, 张纪峰. 多自主体量化趋同与有限数据率趋同综述. 自动化学报, 2013, 39(11): 1805−1811 doi: 10.3724/SP.J.1004.2013.01805Li Tao, Meng Yang, Zhang Ji-Feng. An overview on quantized consensus and consensus with limited data rate of multi-agent systems. Acta Automatica Sinica, 2013, 39(11): 1805−1811 doi: 10.3724/SP.J.1004.2013.01805
|
|
[2]
|
杨洪勇, 郭雷, 张玉玲, 姚秀明. 离散时间分数阶多自主体系统的时延一致性. 自动化学报, 2014, 40(9): 2022−2028Yang Hong-Yong, Guo Lei, Zhang Yu-Ling, Yao Xiu-Ming. Delay consensus of fractional-order multi-agent systems with sampling delays. Acta Automatica Sinica, 2014, 40(9): 2022−2028
|
|
[3]
|
Yao A C. Protocols for secure computations. In: Proceedings of the 23rd Annual Symposium on Foundations of Computer Science. Chicago, IL, USA: IEEE, 1982. 160−164
|
|
[4]
|
Shamir A, How to share a secret. Communication of the ACM, 1979, 22: 612−613 doi: 10.1145/359168.359176
|
|
[5]
|
Kreuter B, Shelat A, Shen C H. Billion-gate secure computation with malicious adversaries. In: Proceedings of the 21st USENIX Conference on Security Symposium. Berkeley, USA: USENIX Association, 2012. 285−300
|
|
[6]
|
Chen W, Cai S. Ad hoc peer-to-peer network architecture for vehicle safety communications. IEEE Communications Magazine, 2005, 43(4): 100−107 doi: 10.1109/MCOM.2005.1421912
|
|
[7]
|
Huang Z, Mitra S, Vaidya N. Differentially private distributed optimization. In: Proceedings of the 2015 International Conference on Distributed Computing and Networking. NewYork, USA: ACM, 2015. 1−10
|
|
[8]
|
Nozari E, Tallapragada P, Cortes J. Differentially private average consensus: obstructions, trade-offs, and optimal algorithm design. Automatica, 2017, 81(7): 221−231
|
|
[9]
|
Katewa V, Pasqualetti F, Gupta V. On privacy vs cooperation in multi-agent systems. International Journal of Control, 2018, 91(7): 1693−1707 doi: 10.1080/00207179.2017.1326632
|
|
[10]
|
Huang Z, Mitra S, Dullerud G. Differentially private iterative synchronous consensus. In: Proceedings of the 2012 ACM Workshop on Privacy in The Electronic Society. NewYork, USA: ACM, 2012. 81−90
|
|
[11]
|
Nozari E, Tallapragada P, Cortes J. Differentially private average consensus with optimal noise selection. IFAC-PapersOnline, 2015, 48(22): 203−205 doi: 10.1016/j.ifacol.2015.10.331
|
|
[12]
|
Manitara N, Hadjicostis C. Privacy-preserving asymptotic average consensus. In: Proceedings of the 2013 European Control Conference (ECC). Zurich, Switzerland: IEEE, 2013. 760−765
|
|
[13]
|
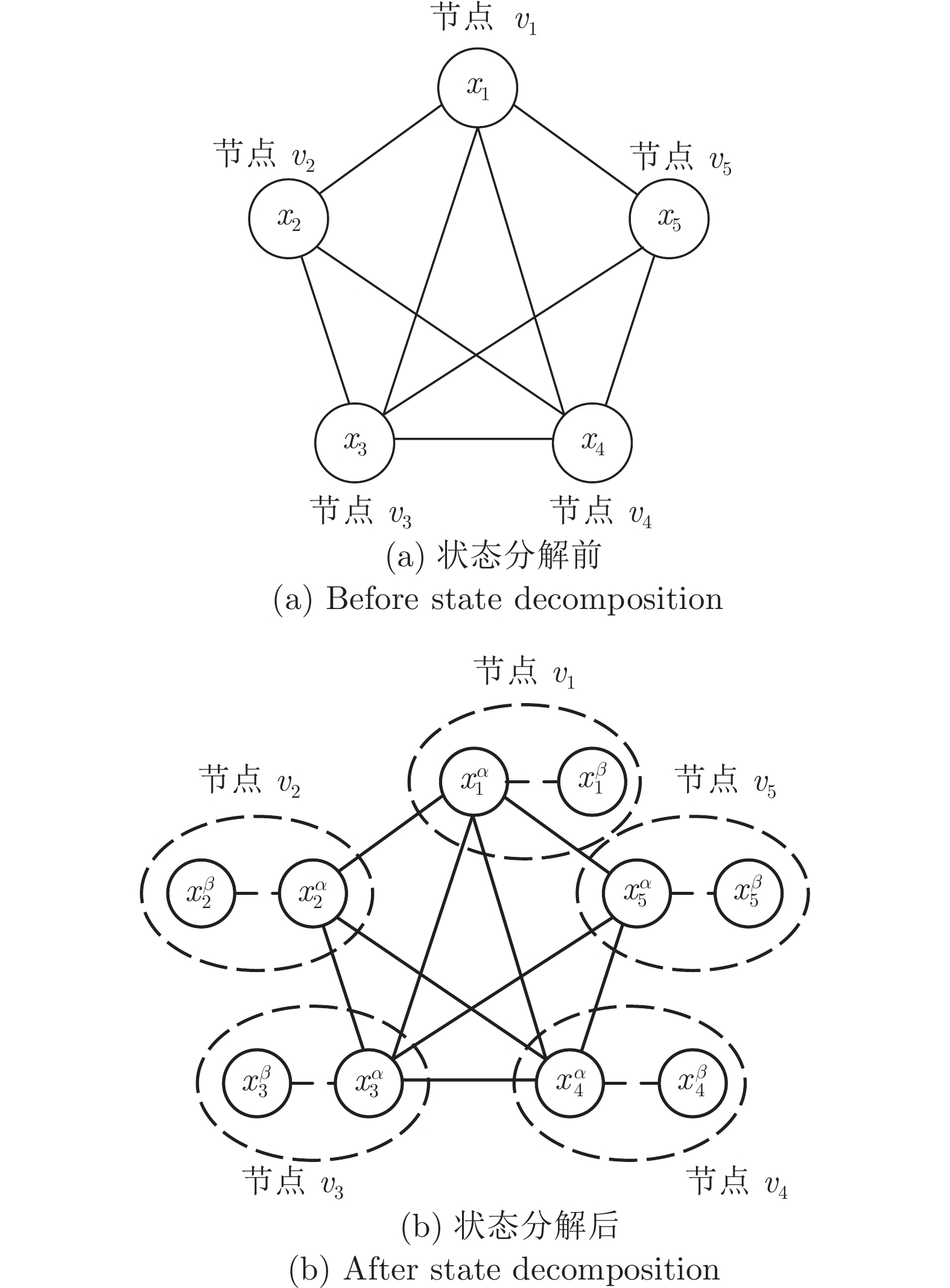
Wang Y. Privacy-preserving average consensus via state decomposition. IEEE Transactions on Automatic Control, 2019, 64(11): 4711−4716 doi: 10.1109/TAC.2019.2902731
|
|
[14]
|
Kia S, Cortes J, Martinez S. Dynamic average consensus under limited control authority and privacy requirements. International Journal of Robust and Nonlinear Control, 2015, 25(13): 1941−1966 doi: 10.1002/rnc.3178
|
|
[15]
|
Pequito S, Kar S, Sundaram S, Aguiar A P. Design of communication networks for distributed computation with privacy guarantees. In: Proceedings of the 2015 54th IEEE Conference on Decision and Control (CDC). Osaka, Japan: IEEE, 2015. 1370−1376
|
|
[16]
|
Alaeddini A, Morgansen K, Mesbahi M. Adaptive communication networks with privacy guarantees. In: Proceedings of the 2017 American Control Conference (ACC). Seattle, USA: IEEE, 2017. 4460−4465
|
|
[17]
|
Gupta N, Chopra N. Confidentiality in distributed average information consensus. In: Proceedings of the 2016 IEEE 55th Conference on Decision and Control (CDC). Las Vegas, USA: IEEE, 2016. 6709−6714
|
|
[18]
|
Kogiso K, Fujita T. Cyber-security enhancement of networked control systems using homomorphic encryption. In: Proceedings of the 2015 54th IEEE Conference on Decision and Control (CDC). Osaka, Japan: IEEE, 2015. 6836−6843
|
|
[19]
|
Shoukry Y, Gatsis K, Alanwar A, Pappas G J, Seshia S A, Srivastava M, et al. Privacy-aware quadratic optimization using partially homomorphic encryption. In: Proceedings of the 2016 IEEE 55th Conference on Decision and Control (CDC). Las Vegas, USA: IEEE, 2016. 5053−5058
|
|
[20]
|
Lagendijk R L, Erkin Z, Barni M. Encrypted signal processing for privacy protection: Conveying the utility of homomorphic encryption and multiparty computation. IEEE Signal Processing Magazine, 2013, 30(1): 82−105 doi: 10.1109/MSP.2012.2219653
|
|
[21]
|
Zhang C, Ahmad M, Wang Y. Admm based privacy-preserving decentralized optimization. IEEE Transactions on Information Forensics and Security, 2019, 14(3): 565−580 doi: 10.1109/TIFS.2018.2855169
|
|
[22]
|
LeBlanc H J, Zhang H, Koutsoukos X, Sundaram S. Resilient asymptotic consensus in robust networks. IEEE Journal on Selected Areas in Communications, 2013, 31(4): 766−781 doi: 10.1109/JSAC.2013.130413
|
|
[23]
|
Wu Y, He X. Secure consensus control for multiagent systems with attacks and communication delays. IEEE/CAA Journal of Automatica Sinica, 2017, 4(1): 136−142 doi: 10.1109/JAS.2016.7510010
|
|
[24]
|
Fiore D, Russo G. Resilient consensus for multi-agent systems subject to differential privacy requirements. Automatica, 2019, 106: 18−26 doi: 10.1016/j.automatica.2019.04.029
|
|
[25]
|
黄锦波, 伍益明, 何熊熊, 常丽萍. 信任节点机制下的异构多智能体系统安全一致性控制. 中国科学: 信息科学, 2019, 49(5): 599−612 doi: 10.1360/N112018-00343Huang Jin-Bo, Wu Yi-Ming, He Xiong-Xiong, Chang Li-Ping. Secure consensus control for heterogeneous multi-agent systems with trusted nodes. Sci Sin Inform, 2019, 49(5): 599−612 doi: 10.1360/N112018-00343
|
|
[26]
|
Usevitch J, Panagou D. Resilient leaderfollower consensus to arbitrary reference values in time-varying graphs. IEEE Transactions on Automatic Control, 2020, 65(4): 1755−1762 doi: 10.1109/TAC.2019.2934954
|
|
[27]
|
He W, Mo Z, Han Q L, Qian F. Secure impulsive synchronization in lipschitztype multi-agent systems subject to deception attacks. IEEE/CAA Journal of Automatica Sinica, 2020, 5(7): 1326−1334
|
|
[28]
|
Fu W, Qin J, Shi Y, Zheng W X, Kang Y. Resilient consensus of discrete-time complex cyber-physical networks under deception attacks. IEEE Transactions on Industrial Informatics, 2020, 16(7): 4868−4877 doi: 10.1109/TII.2019.2933596
|
|
[29]
|
Zhang D, Liu L, Feng G. Consensus of heterogeneous linear multiagent systems subject to aperiodic sampled-data and dos attack. IEEE Transactions on Cybernetics, 2019, 49(4): 1501−1511 doi: 10.1109/TCYB.2018.2806387
|
|
[30]
|
Feng Z, Hu G. Secure cooperative event-triggered control of linear multiagent systems under dos attacks. IEEE Transactions on Control Systems Technology, 2020, 28(3): 741−752 doi: 10.1109/TCST.2019.2892032
|
|
[31]
|
Yang Y, Xu H, Yue D. Observer-based distributed secure consensus control of a class of linear multi-agent systems subject to random attacks. IEEE Transactions on Circuits and Systems I: Regular Papers, 2019, 66(8): 3089−3099 doi: 10.1109/TCSI.2019.2904747
|
|
[32]
|
Xu W, Hu G, Ho D W, Feng Z. Distributed secure cooperative control under denial-of-service attacks from multiple adversaries. IEEE Transactions on Cybernetics, 2020, 50(8): 3458−3467 doi: 10.1109/TCYB.2019.2896160
|
|
[33]
|
Wen G, Wang P, Huang T, Lü J, Zhang F. Distributed Consensus of Layered Multi-Agent Systems Subject to Attacks on Edges. IEEE Transactions on Circuits and Systems I: Regular Papers, 2020, 67(9): 3152−3162 doi: 10.1109/TCSI.2020.2986953
|
|
[34]
|
Zhang H, Fata E, Sundaram S. A notion of robustness in complex networks. IEEE Transactions on Control of Network Systems, 2015, 2(3): 310−320 doi: 10.1109/TCNS.2015.2413551
|
|
[35]
|
Yin X, Tan C, Huang J. Output consensus for networks of heterogeneous linear agents. In: Proceedings of the 2017 36th Chinese Control Conference (CCC). Dalian, China: IEEE, 2017. 7679−7683
|
|
[36]
|
Zhang H, Sundaram S. Robustness of information diffusion algorithms to locally bounded adversaries. In: Proceedings of the 2012 American Control Conference (ACC). Montréal, Canada: IEEE, 2012. 5855−5861
|
|
[37]
|
Olfati-Saber R, Fax J A, Murray R M. Consensus and cooperation in networked multi-agent systems. Proceedings of the IEEE, 2007, 95(1): 215−233 doi: 10.1109/JPROC.2006.887293
|
|
[38]
|
Nedic A, Ozdaglar A, Parrilo P A. Constrained consensus and optimization in multi-agent networks. IEEE Transactions on Automatic Control, 2010, 55(4): 922−938 doi: 10.1109/TAC.2010.2041686
|
|
[39]
|
Yang Y, Li Y, Yue D, Tian Y, Ding X. Distributed secure consensus control with event-triggering for multiagent systems under dos attacks. IEEE Transactions on Cybernetics, DOI: 10.1109/TCYB.2020.2979342.
|




 下载:
下载: