Multi-attribute Index Processing Method of Target Threat Assessment in Ground Combat
-
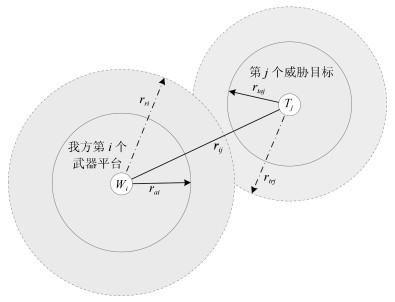
摘要: 评估指标的量化处理是目标威胁评估(Threat assessment, TA)算法应用的基础.本文针对地面作战目标威胁评估指标类型多样和难以量化的问题, 系统地提出了一种多属性威胁指标的量化方法, 并将指标量化结果转化为统一的直觉模糊集(Intuitionistic fuzzy set, IFS)表示形式.研究了地面作战目标威胁评估指标如目标距离、速度、攻击角度、类型、通视条件和作战环境等, 通过模糊评价语言、区间数、实数、三角模糊数等方式进行量化, 最大限度地保留指标不确定信息并降低实际应用的复杂度; 提出了不同表示形式的威胁指标数据与直觉模糊数的转化原则和转化方法, 并给出了理论可行性的数学证明.通过一个地面作战目标威胁评估的多属性指标处理实例, 验证了该方法在多属性指标量化和直觉模糊集表示中的合理性, 说明了该方法能够为目标威胁评估提供科学的评估数据.Abstract: Quantitative processing of evaluation indexes is the application basis of target threat assessment (TA) algorithm. Aiming at the problems that the TA indexes of ground combat targets are various and difficult to quantify, this paper proposes a quantization method of multi-attribute threat indexes systematically, and transforms the quantization results of indexes into a unified intuitionistic fuzzy set (IFS) representation. TA indexes such as target distance, velocity, attack angle, type, visual condition and combat environment are studied. Fuzzy evaluation language, interval number, real number and triangular fuzzy number are used to quantify the indexes in TA. The uncertain information of the indexes is retained with the maximum extent and the complexity of practical applications is reduced. The transformation principle and method that threat indexes in different forms transform into intuitionistic fuzzy number are put forward, and the mathematical proof of theoretical feasibility is given. An example of multi-attribute indexes processing for TA of ground combat targets is given to verify the rationality of the proposed method in quantifying multi-attribute indexes and transforming them into IFS. It shows that the proposed method can provide scientific evaluation data for target TA.
-
Key words:
- Ground combat /
- threat assessment (TA) /
- multi-attribute index /
- intuitionistic fuzzy sets (IFS)
1) 本文责任编委 魏庆来 -
表 1 确定程度的区间值对应关系
Table 1 Determination degree corresponding to interval values
确定程度 $L$ $U$ $c_5$ (十分确定) 0.9 1 $c_4$ (比较确定) 0.6 0.9 $c_3$ (一般) 0.4 0.6 $c_2$ (不太确定) 0.2 0.4 $c_1$ (不确定) 0 0.2 表 2 模糊评价语言标度与IFN的转化
Table 2 Scale of fuzzy evaluation language and transformation to IFN
模糊评价 直觉模糊数 语言标度 $\mu $ $\upsilon $ $\pi $ $\alpha =10$ (极大) 1 0 0 $\alpha =9$ (很大) 0.9 0.05 0.05 $\alpha =8$ (大) 0.8 0.1 0.1 $\alpha =7$ (较大) 0.7 0.15 0.15 $\alpha =6$ (稍大) 0.55 0.3 0.15 $\alpha =5$ (中等) 0.4 0.4 0.2 $\alpha =4$ (稍小) 0.4 0.45 0.15 $\alpha =3$ (较小) 0.3 0.55 0.15 $\alpha =2$ (小) 0.2 0.7 0.1 $\alpha =1$ (很小) 0.1 0.85 0.05 $\alpha =0$ (极小) 0 1 0 表 3 目标威胁评估指标参数
Table 3 Index parameters of target threat assessment
目标 $f_1$ $f_2$ $f_3$ $f_4$ $f_5$ $f_6$ $f_7$ $f_8$ $f_9$ $T_1$ 大(十分确定) 较大(比较确定) 大(比较确定) 大(比较确定) [25, 30] [120, 150] 2 500 [0.7, 1] 良 $T_2 $ 较大(比较确定) 大(一般) 大(比较确定) 较大(比较确定) [30, 35] [180, 210] 2 000 [0.3, 0.7] 良 $T_3$ 中等(比较确定) 稍小(十分确定) 较大(一般) 较大(一般) [15, 20] [150, 180] 2 200 [0.7, 1] 良 $T_4$ 较大(比较确定) 小(不确定) 大(一般) 中等(比较确定) [15, 20] [90, 150] 1 800 [0.3, 0.7] 良 $T_5$ 很大(十分确定) 大(比较确定) 很大(一般) 很大(十分确定) [100, 150] [135, 180] 4 200 [0.7, 1] 优 $T_6$ 很小(一般) 小(比较确定) 很小(十分确定) 很小(比较确定) [5, 8] [150, 210] 800 [0.7, 1] 良 表 4 目标距离威胁度
Table 4 Threat degree of target distance to IFN
目标 打击距离 有效侦察距离 距离威胁度 直觉模糊数表示 $T_1$ 2 500 3 500 0.40 $\left\langle 0.47, 0.33 \right\rangle$ $T_2$ 2 500 3 500 0.52 $\left\langle0.61, 0.19\right\rangle$ $T_3$ 2 400 3 200 0.45 $\left\langle0.53, 0.27\right\rangle$ $T_4$ 3 000 3 500 0.64 $\left\langle0.75, 0.05\right\rangle$ $T_5$ 5 000 6 000 0.68 $\left\langle0.8, 0\right\rangle$ $T_6$ 800 1 000 0.30 $\left\langle0.35, 0.45\right\rangle$ 表 5 目标攻击角度威胁度
Table 5 Threat degree of target attack angle
目标 目标攻击角度 我方武器攻击角度 目标攻击角度威胁度 直觉模糊数表示 $T_1$ [120, 150] [$-15$, 15] [0.29, 0.46] $\left\langle0.41, 0.35\right\rangle$ $T_2$ [180, 210] [0, 30] [0.50, 0.67] $\left\langle0.71, 0.06\right\rangle$ $T_3$ [150, 180] [$-30$, 0] [0.33, 0.5] $\left\langle0.47, 0.29\right\rangle$ $T_4$ [90, 150] [$-15$, 15] [0.21, 0.46] $\left\langle0.29, 0.35\right\rangle$ $T_5$ [135, 180] [$-45$, 0] [0.25, 0.5] $\left\langle0.35, 0.29\right\rangle$ $T_6$ [150, 210] [15, 45] [0.46, 0.71] $\left\langle0.65, 0\right\rangle$ 表 6 目标速度威胁度
Table 6 Threat degree of target speed
目标 目标速度 速度威胁度 直觉模糊数表示 $T_1$ [25, 30] [0.50, 0.60] $\left\langle0.67, 0.2\right\rangle$ $T_2$ [30, 35] [0.60, 0.70] $\left\langle0.8, 0.07\right\rangle$ $T_3$ [15, 20] [0.30, 0.40] $\left\langle0.4, 0.47\right\rangle$ $T_4$ [15, 20] [0.30, 0.40] $\left\langle0.4, 0.47\right\rangle$ $T_5$ [100, 150] [0.50, 0.75] $\left\langle0.67, 0\right\rangle$ $T_6$ [5, 10] [0.33, 0.53] $\left\langle0.44, 0.29\right\rangle$ 表 7 目标威胁评估指标参数
Table 7 Index parameters of target threat assessment
目标 $f_1$ $f_2$ $f_3$ $f_4$ $f_5$ $f_6$ $f_7$ $f_8$ $f_9$ $T_1$ $\left\langle0.79, 0.11\right\rangle$ $\left\langle0.64, 0.19\right\rangle$ $\left\langle0.79, 0.11\right\rangle$ $\left\langle0.79, 0.11\right\rangle$ $\left\langle0.67, 0.2\right\rangle$ $\left\langle0.41, 0.35\right\rangle$ $\left\langle0.47, 0.33\right\rangle$ $\left\langle0.7, 0\right\rangle$ $\left\langle0.5, 0.3\right\rangle$ $T_2$ $\left\langle0.64, 0.19\right\rangle$ $\left\langle0.65, 0.2\right\rangle$ $\left\langle0.74, 0.14\right\rangle$ $\left\langle0.64, 0.19\right\rangle$ $\left\langle0.8, 0.07\right\rangle$ $\left\langle0.71, 0.06\right\rangle$ $\left\langle0.61, 0.19\right\rangle$ $\left\langle0.3, 0.3\right\rangle$ $\left\langle0.5, 0.3\right\rangle$ $T_3$ $\left\langle0.4, 0.4\right\rangle$ $\left\langle0.4, 0.45\right\rangle$ $\left\langle0.65, 0.2\right\rangle$ $\left\langle0.65, 0.2\right\rangle$ $\left\langle0.4, 0.47\right\rangle$ $\left\langle0.47, 0.29\right\rangle$ $\left\langle0.53, 0.27\right\rangle$ $\left\langle0.7, 0\right\rangle$ $\left\langle0.5, 0.3\right\rangle$ $T_4$ $\left\langle0.64, 0.19\right\rangle$ $\left\langle0.21, 0.68\right\rangle$ $\left\langle0.65, 0.2\right\rangle$ $\left\langle0.4, 0.4\right\rangle$ $\left\langle0.4, 0.47\right\rangle$ $\left\langle0.29, 0.35\right\rangle$ $\left\langle0.75, 0.05\right\rangle$ $\left\langle0.3, 0.3\right\rangle$ $\left\langle0.5, 0.3\right\rangle$ $T_5$ $\left\langle0.89, 0.06\right\rangle$ $\left\langle0.74, 0.14\right\rangle$ $\left\langle0.76, 0.14\right\rangle$ $\left\langle0.89, 0.06\right\rangle$ $\left\langle0.67, 0\right\rangle$ $\left\langle0.35, 0.29\right\rangle$ $\left\langle0.8, 0\right\rangle$ $\left\langle0.7, 0\right\rangle$ $\left\langle0.7, 0.1\right\rangle$ $T_6$ $\left\langle0.27, 0.58\right\rangle$ $\left\langle0.26, 0.61\right\rangle$ $\left\langle0.12, 0.82\right\rangle$ $\left\langle0.19, 0.7\right\rangle$ $\left\langle0.44, 0.29\right\rangle$ $\left\langle0.65, 0\right\rangle$ $\left\langle0.35, 0.45\right\rangle$ $\left\langle0.7, 0\right\rangle$ $\left\langle0.5, 0.3\right\rangle$ 表 8 目标威胁评估结果
Table 8 Target threat assessment results
$S_{i}^{+}$ $[0.863, 0.858, 0.745, 0.699, 0.950, 0.601]$ $S_{i}^{-}$ $[0.646, 0.651, 0.764, 0.810, 0.559, 0.908]$ $p_i$ $[0.572, 0.569, 0.494, 0.463, 0.629, 0.398]$ 排序 $T_5>T_1> T_2> T_3> T_4>T_6$ -
[1] Kong D P, Chang T Q, Wang Q D, et al. A threat assessment method of group targets based on interval-valued intuitionistic fuzzy multi-attribute group decision-making. Applied Soft Computing, 2018, 67(6): 350-369 [2] Deng Y. A threat assessment model under uncertain environment. Mathematical Problems in Engineering, 2015, (9): 1-12 [3] Huang J, Li B C, Zhao Y J. Target threat assessment based on intuitionistic fuzzy sets choquet integral. Applied Mechanics and Materials, 2013, 433-435(9): 736-743 [4] Roux J N, Van Vuuren J H. Threat evaluation and weapon assignment decision support: A review of the state of the art. ORiON, 2007, 23(2): 151-187 [5] Lee H, Choi B J, Kim C O, et al. Threat evaluation of enemy air fighters via neural network-based Markov chain modeling. Knowledge-Based Systems, 2017, 116(1): 49-57 [6] 刘敬蜀, 姜文志, 雷宇曜, 等.动态火力接入下要地防空作战目标威胁评估.北京航空航天大学学报, 2016, 42(7): 1422-1431 https://www.cnki.com.cn/Article/CJFDTOTAL-BJHK201607013.htmLiu Jing-Shu, Jiang Wen-Zhi, Lei Yu-Yao, et al. Threat evaluation of air-targets for key positions air-defense under dynamic fire access. Journal of Beijing University of Aeronautics and Astronautics, 2016, 42(7): 1422-1431 https://www.cnki.com.cn/Article/CJFDTOTAL-BJHK201607013.htm [7] Looney C G, Liang L R. Cognitive situation and threat assessments of ground battlespaces. Information Fusion, 2003, 4(4): 297-308 doi: 10.1016/S1566-2535(03)00044-7 [8] A. M G. The magical number seven plus or minus two: some limits on our capacity for processing information. Psychological Review, 1956, 63(2): 81-97 doi: 10.1037/h0043158 [9] Maccrimmon K R. Decisionmaking among multiple- attribute alternatives: a survey and consolidated approach. Report RM-4823-ARPA, Santa Monica: RAND Corporation, 1968. [10] Naseem A, Shah S T H, Khan S A, et al. Decision support system for optimum decision making process in threat evaluation and weapon assignment: Current status, challenges and future directions. Annual Reviews in Control, 2017, 43: 169-187 doi: 10.1016/j.arcontrol.2017.03.003 [11] 毛红保, 冯卉, 张亮, 等.基于MADM组合赋权的空中目标威胁评估方法.信息工程大学学报, 2014, 15(3): 281-285 https://www.cnki.com.cn/Article/CJFDTOTAL-XXGC201403005.htmMao Hong-Bao, Feng Hui, Zhang Liang, et al. Aerial targets threat evaluation method based on combination weighting for MADM. Journal of Information Engineering University, 2014, 15(3): 281-285 https://www.cnki.com.cn/Article/CJFDTOTAL-XXGC201403005.htm [12] 陈维义, 王少蕾, 周菲.基于加权核主成分TOPSIS方法的舰艇防空威胁评估.海军工程大学学报, 2014, 26(1): 87-91 https://www.cnki.com.cn/Article/CJFDTOTAL-HJGX201401018.htmChen Wei-Yi, Wang Shao-Lei, Zhou Fei. Threat evaluation of air targets to ships in air defense based on weighted KPCA-TOPSIS. Journal of Naval University of Engineering, 2014, 26(1): 87-91 https://www.cnki.com.cn/Article/CJFDTOTAL-HJGX201401018.htm [13] Atanassov K T. Intuitionistic fuzzy sets. Fuzzy Sets and Systems, 1986, 20(1): 87-96 doi: 10.1016/S0165-0114(86)80034-3 [14] Szmidt E, Kacprzyk J. Entropy for intuitionistic fuzzy sets. Fuzzy Sets and Systems, 2001, 118(3): 467-477 doi: 10.1016/S0165-0114(98)00402-3 [15] Zhang H, Yu L. New distance measures between intuitionistic fuzzy sets and interval-valued fuzzy sets. Information Sciences, 2013, 245(10): 181-196 [16] Xu Z S. Some similarity measures of intuitionistic fuzzy sets and their applications to multiple attribute decision making. Fuzzy Optimization and Decision Makings, 2007, 6(2): 109-121 doi: 10.1007/s10700-007-9004-z [17] Guo K. Knowledge measure for Atanassov$'$s intuitionistic fuzzy sets. IEEE Transactions on Fuzzy Systems, 2016, 24(5): 1072-1078 doi: 10.1109/TFUZZ.2015.2501434 [18] Xu Z S. Intuitionistic fuzzy aggregation operators. IEEE Transactions on Fuzzy Systems, 2007, 15(6): 1179-1187 doi: 10.1109/TFUZZ.2006.890678 [19] Liu P, Chen S M. Group decision making based on heronian aggregation operators of intuitionistic fuzzy numbers. IEEE Transactions on Cybernetics, 2017, 47(9): 2514-2530 doi: 10.1109/TCYB.2016.2634599 [20] Xu Z S. Approaches to multiple attribute group decision making based on intuitionistic fuzzy power aggregation operators. Knowledge-Based Systems, 2011, 24(6): 749-760 doi: 10.1016/j.knosys.2011.01.011 [21] Nguyen H. A new knowledge-based measure for intuitionistic fuzzy sets and its application in multiple attribute group decision making. Expert Systems with Applications, 2015, 42(22): 8766-8774 doi: 10.1016/j.eswa.2015.07.030 [22] 王毅, 刘三阳, 张文, 等.属性权重不确定的直觉模糊多属性决策的威胁评估方法.电子学报, 2014, 42(12): 2509-2514 https://www.cnki.com.cn/Article/CJFDTOTAL-DZXU201412025.htmWang Yi, Liu San-Yang, Zhang Wen, et al. Threat assess ment method with uncertain attribute weight based on intuitionistic fuzzy multi-attribute decision. Acta Electronica Sinica, 2014, 42(12): 2509-2514 https://www.cnki.com.cn/Article/CJFDTOTAL-DZXU201412025.htm [23] 武华, 苏秀琴.基于群广义直觉模糊软集的空袭目标威胁评估方法.控制与决策, 2015, 30(8): 1462-1468 https://www.cnki.com.cn/Article/CJFDTOTAL-KZYC201508019.htmWu Hua, Su Xiu-Qin. Threat assessment of aerial targets based on group generalized intuitionistic fuzzy soft sets. Control and Decision, 2015, 30(8): 1462-1468 https://www.cnki.com.cn/Article/CJFDTOTAL-KZYC201508019.htm [24] 张堃, 王雪, 张才坤, 等.基于IFE动态直觉模糊法的空战目标威胁评估.系统工程与电子技术, 2014, 36(4): 697-701 https://www.cnki.com.cn/Article/CJFDTOTAL-XTYD201404016.htmZhang Kun, Wang Xue, Zhang Cai-Kun, et al. Evaluating and sequencing of air target threat based on IFE and dynamic intuitionistic fuzzy sets. Systems Engineering and Electronics, 2014, 36(4): 697-701 https://www.cnki.com.cn/Article/CJFDTOTAL-XTYD201404016.htm [25] 郭辉, 徐浩军, 刘凌.基于区间数TOPSIS法的空战目标威胁评估.系统工程与电子技术, 2009, 31(12): 2914-2917 https://www.cnki.com.cn/Article/CJFDTOTAL-XTYD200912028.htmGuo Hui, Xu Hao-Jun, Liu Ling. Threat assessment for air combat target based on interval TOPSIS. Systems Engineering and Electronics, 2009, 31(12): 2914-2917 https://www.cnki.com.cn/Article/CJFDTOTAL-XTYD200912028.htm [26] 徐泽水.对方案有偏好的三角模糊数型多属性决策方法研究.系统工程与电子技术, 2002, 24(8): 9-12 https://www.cnki.com.cn/Article/CJFDTOTAL-XTYD200208003.htmXu Zhe-Shui. Study on method for triangular fuzzy number-based multi-attribute decision making with preference information on alternatives. Systems Engineering and Electronics, 2002, 24(8): 9-12 https://www.cnki.com.cn/Article/CJFDTOTAL-XTYD200208003.htm [27] Zhai Y L, Xu Z S, Liao H C. Probabilistic linguistic vector-term set and its application in group decision making with multi-granular linguistic information. Applied Soft Computing, 2016, 49(12): 801-816 [28] Xu Z S. Deviation measures of linguistic preference relations in group decision making. Omega, 2005, 33(3): 249-254 doi: 10.1016/j.omega.2004.04.008 [29] 黄家辉, 冯冬芹, 王虹鉴.基于攻击图的工控系统脆弱性量化方法.自动化学报, 2016, 42(5): 792-798 doi: 10.16383/j.aas.2016.c150517Huang Jia-Hui, Feng Dong-Qin, Wang Hong-Jian. A method for quantifying vulnerability of industrial control system based on attack graph. Acta Automatica Sinica, 2016, 42(5): 792-798 doi: 10.16383/j.aas.2016.c150517 [30] Kumar S, Tripathi B K. Modelling of threat evaluation for dynamic targets using Bayesian network approach. Procedia Technology, 2016, 24: 1268-1275 doi: 10.1016/j.protcy.2016.05.112 [31] Naeem H, Masood A. An optimal dynamic threat evaluation and weapon scheduling technique. Knowledge-Based Systems, 2010, 23(4): 337-342 doi: 10.1016/j.knosys.2009.11.012 [32] Chen S M, Cheng S H, Lan T C. Multicriteria decision making based on the TOPSIS method and similarity measures between intuitionistic fuzzy values. Information Sciences, 2016, 367-368(11): 279-295 -




 下载:
下载:



