Privacy-preserving Average Consensus Control for Multi-agent Systems Under DoS Attacks
-
摘要: 均值趋同是一种广泛应用于分布式计算和控制的算法, 旨在系统通过相邻节点间信息交互、更新, 最终促使系统中所有节点以它们初始值的均值达成一致. 研究拒绝服务(Denial-of-service, DoS)攻击下的分布式离散时间多智能体系统均值趋同问题. 首先, 给出一种基于状态分解思想的分布式网络节点状态信息处理机制, 可保证系统中所有节点输出值的隐私. 然后, 利用分解后的节点状态值及分析给出的网络通信拓扑条件, 提出一种适用于无向通信拓扑的多智能体系统均值趋同控制方法. 理论分析表明, 该方法能够有效抵御DoS攻击的影响, 且实现系统输出值均值趋同. 最后, 通过仿真实例验证了该方法的有效性.Abstract: Average consensus is a widely used algorithm for distributed computing and control, where all the nodes in the network constantly communicate and update their states in order to achieve an agreement. In this paper, we study the average consensus problem for discrete-time multi-agent systems under DoS attacks. First, a distributed network node state value processing mechanism based on state decomposition is given, which can ensure the privacy of the output values of all nodes in the system. Then, through using the decomposed node state values and the network topology conditions given by the analysis, an average output consensus control law for distributed discrete-time multi-agent systems is proposed. Theoretical analysis shows that the proposed method can effectively resist the influence of DoS attacks on the system, and achieve the convergence of the average value of system initial outputs. Finally, numerical examples are presented to show the validity of the proposed method.
-
Key words:
- Multi-agent systems /
- average consensus /
- denial-of-service attack /
- privacy-preserving /
- cyber security
-
多智能体系统是由多个具有一定传感、计算、执行和通信能力的智能个体组成的网络系统, 作为分布式人工智能的重要分支, 已成为解决大型、复杂、分布式及难预测问题的重要手段[1-2]. 趋同问题作为多智能体系统分布式协调控制领域中一个最基本的研究课题, 是指在没有协调中心的情况下, 系统中每个节点仅根据相互间传递的信息, 将智能体动力学与网络通信拓扑耦合成复杂网络, 并设计合适的分布式控制方法, 从而在有限时间内实现所有节点状态值的一致或同步.
然而具备分布式网络特点的多智能体系统由于普遍规模庞大, 单个节点结构简单且节点地理位置分散等原因, 使得系统中易产生脆弱点, 这就使其在推广应用中面临两项基本挑战: 1)节点状态信息的隐私泄露问题; 2)节点或节点间的通信链路可能会遭受网络攻击的问题, 如欺骗攻击、拒绝服务(Denial-of-service, DoS)攻击等.
针对节点状态信息的隐私泄露问题, 即在考虑多智能体网络趋同的同时, 保证系统中节点的初始状态值不被泄露, 已有较多研究人员开展相关的工作. 其中, 有学者借助于传统的安全多方计算方法, 例如Yao等[3]提出混淆电路算法, Shamir等[4]提出秘钥共享算法等. 然而这类通用的隐私保护方法因计算和通信消耗较大, 不适用于单个智能体节点结构较为简单的分布式系统, 尤其是受到硬实时约束的一类多智能体系统应用. 如上述的混淆电路的计算延迟为秒级[5], 而对于多智能体系统一些典型应用如多无人飞行器编队的实时控制, 其容许的计算延迟仅为毫秒级[6]. 针对多智能体系统均值趋同过程中节点信息泄露问题, 有研究人员提出了一系列专门的隐私保护策略[7-10]. 这些方法大多基于模糊处理的思想, 即通过加入噪声来掩盖真实的状态值. 其中一种常用的手段是差分隐私方法[11], 然而这种差分隐私下的模糊处理方法会影响最终趋同值的精度, 即使系统无法收敛到精确的节点初始状态的平均值. 最近文献[12]提出的一种基于相关噪声混淆技术的改进方法, 克服了传统差分隐私方法中精度下降的问题, 但却需要较多的算力. 最近的文献[13]采用一种基于状态分解的方法, 将每个节点的初始状态分解为两个随机的子状态, 只令其中一个子状态参与相邻节点间的信息交互, 而另一子状态保留在本节点内部, 不参与邻居间信息传递. 只要两个随机子状态的和满足特定条件, 在作者所设计的趋同算法下, 系统能够达成均值趋同, 且保护每个节点的状态信息不被泄露.
此外, 有学者研究基于可观测性的方法用来保护多智能体系统中节点的隐私[14-16]. 基本思想是设计网络的交互拓扑结构以最小化某个节点的观测性, 本质上相当于最小化该节点推断网络中其他节点初始状态的能力. 然而, 这类基于可观测性的方法仍然存在隐私泄露的风险. 为了提高对隐私攻击的抵御能力, 另一种常见的方法是使用加密技术. 然而, 虽然基于密码学的方法可以很容易地在聚合器或第三方[17]的帮助下实现隐私保护, 例如基于云的控制或运算[18-20], 但是由于分散密钥管理的困难, 在没有聚合器或第三方的情况下, 将基于密码学的方法应用到完全分散的均值趋同问题是很困难的. 同时, 基于密码学的方法也将显著增加通信和计算开销[21], 往往不适用于资源有限或受硬实时约束的分布式网络控制系统.
以上的工作均是在安全的通信环境下完成的, 然而在实际应用场景中, 由于物理设备和通信拓扑结构都有可能遭受网络攻击, 导致以往有关多智能体系统趋同研究的失效, 这使得针对多智能体系统在网络攻击下的趋同研究发展迅速, 并取得了一些显著成果[22-26]. 目前多智能体系统中常见的网络攻击主要有两种形式: 欺骗攻击[22, 25, 27-28]和DoS攻击[29-33]. 其中DoS攻击是多智能体系统中最常见也是最容易实现的攻击形式, 只要攻击者掌握系统元器件之间的通信协议, 即可利用攻击设备开展干扰、阻塞通信信道、用数据淹没网络等方式启动DoS攻击. 在DoS攻击影响下, 智能体间交互的状态信息因传递受阻而致使系统无法达成一致. 近年来, 研究者们从控制理论的角度对DoS攻击下的系统趋同问题进行了研究. 其中, 有研究人员通过构建依赖于参数的通用Lyapunov函数设计一种趋同方法[31], 使其能够适用于因通信链路存在随机攻击导致通信拓扑随机切换的情况. 此外, 有研究者通过设计一个独立于全局信息的可靠分布式事件触发器[32], 很好地解决了大规模DoS攻击下的一致性问题. 更有研究者开始研究异构多智能体系统在通信链路遭受攻击时的趋同问题[33], 通过设计基于观测器的控制器, 实现在通信链路存在DoS攻击时两层节点间的趋同问题. 而在本文中, 考虑多智能体之间通信链路遭受DoS攻击的情况, 通过攻击开始时刻与攻击链路矩阵刻画DoS攻击模型, 通过增强网络拓扑以满足所谓的
$ r $ -鲁棒图来刻画信息流的局部冗余量[34], 从而抵御DoS攻击的影响.然而, 针对趋同问题, 将网络攻击和隐私保护两者结合起来考虑的研究还鲜有见文献报道. 2019年Fiore等[24]率先开展了同时考虑隐私保护和网络攻击的研究工作, 但所得成果仍存在一定的局限性: 1)所提方法虽能保护节点隐私且最终达成状态值趋同, 却无法确保系统达成均值趋同; 2)作者仅考虑了欺骗攻击下的控制器设计问题, 因此所得结论并不适用于网络中存有DoS攻击的系统.
基于上述观察与分析, 本文主要致力于研究DoS攻击下具备节点信息隐私保护的多智能体系统均值趋同问题, 从而补充现有趋同算法的相关结果. 同时, 考虑实际环境对测量条件等的限制, 不易直接获取节点的真实状态值[35], 为此本文围绕节点的输出值, 即通过观测矩阵获取的系统输出
$ y $ , 进行趋同控制器的设计工作. 本文的主要贡献包括:1)针对DoS攻击在多智能体系统分布式协同控制中的攻击特性和发生范围, 及对网络拓扑连通性的影响, 建立相应数学模型;
2)针对一类DoS攻击下的无向通信网络多智能体系统, 提出一种基于状态分解的节点信息隐私保护策略. 当满足特定条件时, 所提策略可确保系统输出状态不被窃听者准确推断出来;
3)针对DoS攻击的影响, 分析给出了系统中节点通信拓扑的鲁棒性条件, 并据此设计一种基于输出量测值
$ y $ 的分布式控制方法, 理论分析并证明系统可容忍特定数目的链路遭受DoS破坏, 并实现输出均值趋同.本文内容结构为: 第1节介绍本文所需要用到的图论知识, 网络拓扑图的相关性质以及均值趋同算法; 第2节主要对DoS攻击模型和拟解决问题进行描述; 第3节提出系统在DoS攻击下的隐私保护均值趋同控制方法, 并分别对在攻击下的网络拓扑鲁棒性、系统收敛性以及隐私保护能力进行分析; 第4节通过一组仿真实例验证算法的有效性; 第5节是总结与展望.
1. 预备知识
1.1 图论知识
考虑由
$ M $ 个智能体组成的多智能体系统, 节点之间为双向传递信息, 其通信网络可抽象地用一个无向加权图${\cal G} = ({\cal V},{\cal E},A)$ 表示. 其中${\cal V} = \{v_1,v_2,\cdots, v_M\}$ 表示节点集合,$ {\cal E}\subset{\cal V}\times{\cal V} $ 表示边集. 两个节点之间的连接关系用邻接矩阵(权重矩阵)${\boldsymbol{A}} = \big[a_{ij}\big]\in{\bf{R}}^{M\times{M}}$ 表示, 如果$ (v_j,v_i)\in {\cal E} $ , 则$ a_{ij}>0 $ ; 否则$ a_{ij} = 0 $ . 在无向图中, 邻接矩阵是对称的, 即如果$ (v_j,v_i)\in {\cal E} $ , 则同时有$ (v_i,v_j)\in {\cal E} $ , 且$ a_{ij} = a_{ji} $ . 本文不考虑节点自环情况, 即令$ a_{ii} = 0 $ . 节点$ v_i $ 的邻居集合表示为$ {\cal N}_i = \{v_j\in{\cal V}|(v_j,v_i)\in{\cal E}\} $ . 无向图$ {\cal G} $ 对应的Laplacian矩阵为${\boldsymbol{L}} = {\boldsymbol{D}}-A$ , 其中D为度矩阵, 定义为:$$ {\boldsymbol{D}} = \mathrm{diag}\left\{\sum\limits_{j = 1}^Ma_{1j},\sum\limits_{j = 1}^Ma_{2j},\cdots,\sum\limits_{j = 1}^Ma_{Mj}\right\} $$ 除了上述无向图的基本知识, 本文的研究工作还用到了r-可达集合和r-鲁棒图的概念. 这两个概念最早由文献[36]提出, 随后被文献[22, 27]等利用并扩展, 主要用于分析节点间拓扑抵御网络攻击的鲁棒性. 经笔者少许修改, 具体定义如下:
定义1[36]. r-可达集合: 对于图
$ {\cal G} = ({\cal V},{\cal E}) $ 及其中一非空子集$ {\cal S}\subset{\cal V} $ , 如果$ {\cal S} $ 中至少有一个节点$ v_i $ 在集合$ {\cal N}_i\setminus{\cal S} $ 中有不少于$ r $ 个节点, 则称$ {\cal S} $ 为r-可达集合.定义 2[36]. r-鲁棒图: 对于图
$ {\cal G} = ({\cal V},{\cal E}) $ , 如果对$ {\cal V} $ 中任意一对非空子集$ {\cal S}_1,{\cal S}_2\subset{\cal V} $ ,$ {\cal S}_1\cap{\cal S}_2 = \emptyset $ , 保证至少有一个子集为r-可达集合, 则称$ {\cal G} $ 为r-鲁棒图.以下是一些关于r-鲁棒图的基本性质.
引理1[22]. 考虑一个r-鲁棒图
$ {\cal G} = ({\cal V},{\cal E}) $ , 令$ \hat{{\cal G}} $ 表示$ {\cal G} $ 中每个节点至多移除$ s\; (s < r) $ 条边后的图, 则$ \hat{{\cal G}} $ 是一个$ (r-s) $ -鲁棒图.引理2[22]. 对于一个无向图
$ {\cal G} $ , 如果$ {\cal G} $ 满足1-鲁棒图, 则有$ {\cal G} $ 为连通图.1.2 均值趋同算法
考虑有
$ M $ 个节点组成的无向加权多智能体系统. 为了让系统实现均值趋同, 也就是所有节点的状态$ x_i[k] $ 最终收敛到它们初始状态的平均值${\sum\nolimits_ {i = 1}^Mx_i[0]}/{M}$ , 根据文献[13, 37], 其节点动态更新方程可设计为:$$ {x_i}[k + 1] = x_i[k] + \varepsilon\sum\limits_{v_j\in {\cal N}_i}{a_{ij}(x_j[k]-x_i[k])} $$ (1) 式中,
$ x_i[k] $ 为节点$ v_i $ 在$ k $ 时刻的状态值,$\varepsilon\in(0,{1}/{\Delta})$ 为系统增益系数,$ \Delta $ 通常定义为:$$ \Delta := \max\limits_{i = 1,2,\cdots,M}|{\cal N}_i| $$ (2) 文献[38]表明, 当系统拓扑满足连通图, 且存在
$ \eta > 0 $ 使得$ \eta\leq a_{ij} < 1 $ 时, 系统可在更新规则(1)下实现均值趋同, 即:$$ \mathop {\lim }\limits_{k \to + \infty } {x_i}[k] = \frac{{\sum\limits_{i = 1}^M {{x_i}[0]} }}{M},{\kern 1pt} {\kern 1pt} {\kern 1pt} {\kern 1pt} \forall {v_i} \in {\cal V} $$ (3) 2. 问题描述
本文研究对象为如下
$ M $ 个智能个体组成的一阶离散时间多智能体系统, 其动力学模型为:$$ \left\{ {\begin{aligned} &{x_i[k + 1] = x_i[k] + u_i}\\ &{y_i[k] = n{C}_ix_i[k],\; \; {v_i} = 1,2,\cdots,M} \end{aligned}} \right. $$ (4) 式中,
$x_i[k] \in {\bf{R}}^N$ 为系统的状态值,$ u_i $ 为控制输入,$y_i[k]\in {{\bf{R}}}^Q$ 为系统经通信链路传输得到的量测信号, 需要注意的是, 由于通信链路中存在DoS攻击,$y_i[k]$ 可能遭受影响而无法被邻居节点接收到.$nC_i \in{{\bf{R}}^{Q \times N}}$ 为观测矩阵, 其中$ n $ 为从观测矩阵中抽取出的系数,$n\in {\bf R}_ +$ 为大于0的正实数.2.1 攻击模型
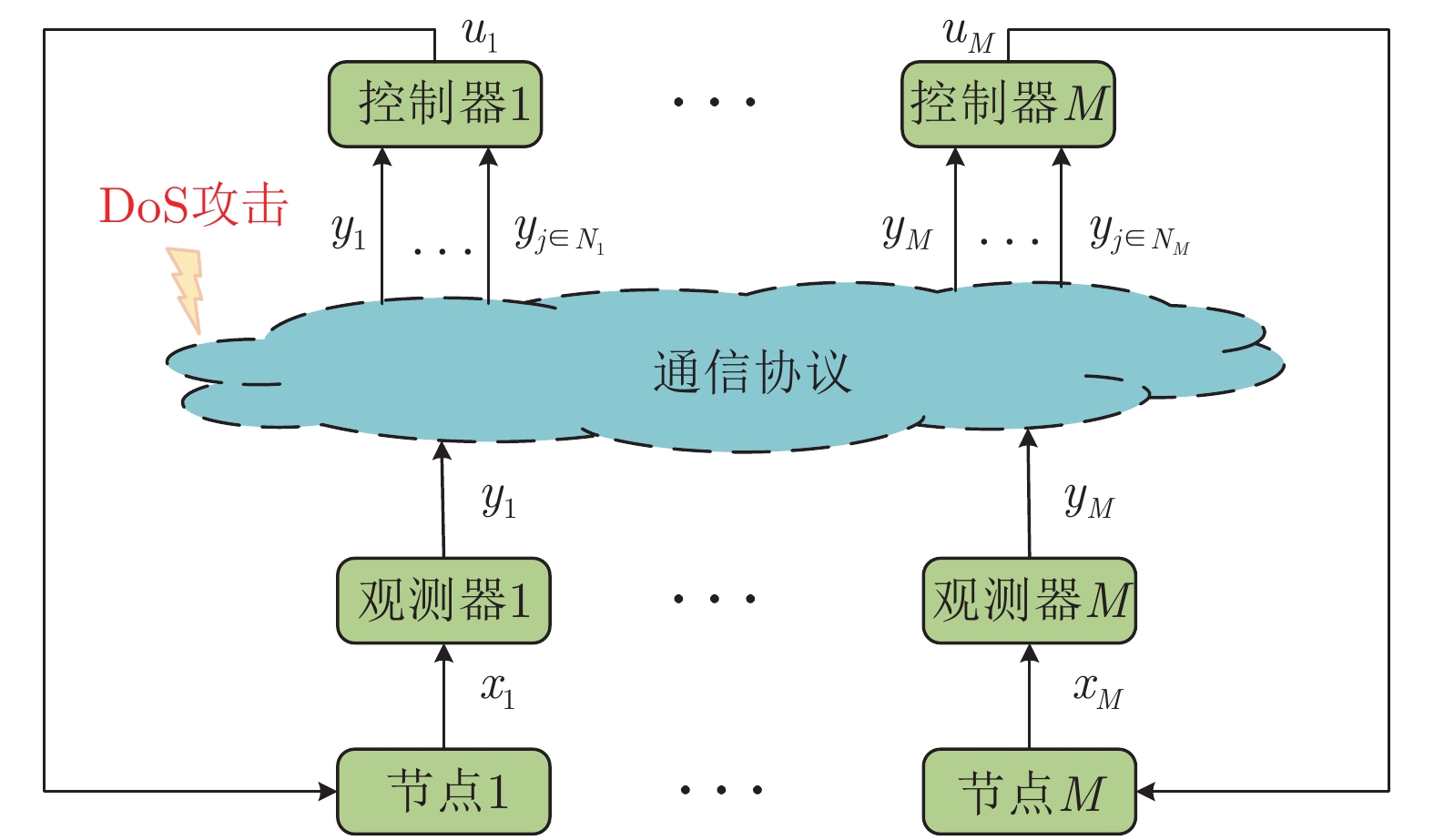
本文所讨论的DoS攻击表现为某种传输尝试失败的情况[39], 其存在于多智能体系统中各智能体之间的通信链路中, 即当通信图中两个节点间的链路发生DoS攻击时, 其通信链路将会被切断, 此时两个节点无法通过该链路进行信息交互, 进而达到攻击多智能体系统的目的. 在多智能体系统分布式协同控制中, 运载节点输出量测值的通信链路遭遇DoS攻击的示意图如图1所示.
本文以Adeversory
$(P,k_0)$ 刻画系统遭遇DoS攻击的情况. 其中$P = \big[p_{ij}[k]\big] \in{\bf {R}}^{M\times{M}}$ 表示攻击状态矩阵, 当节点$ v_i $ 和节点$ v_j $ 之间在$ k $ 时刻发生DoS攻击时,$ p_{ij}[k] = 0 $ ; 否则$ p_{ij}[k] = 1 $ .$ k_0 $ 为系统遭遇DoS攻击的开始时刻.考虑攻击者资源的有限, 本文假设攻击发生范围满足f-本地有界[22]的定义, 该假设在文献[22-23, 25]中被广泛采用. 结合DoS攻击, 具体定义如下:
定义3 (f-本地有界DoS攻击) . 对于系统中的任一节点, 如果与其相邻节点的通信链路中, 任意时刻遭遇DoS攻击的链路条数至多不超过
$ f $ 条, 则称此类攻击模型为f-本地有界DoS攻击.2.2 系统假设
结合上述给出的Adeversory
$(P,k_0)$ 和攻击发生范围模型, 本文对所研究的系统作出如下假设:假设1. 系统中任意一个节点的通信链路中在任意时刻至多有
$ f $ 条链路同时遭受DoS攻击, 即满足定义$ 3 $ 攻击模型. 具体地, 则对于任意$ v_i \in {\cal V} $ , 在任意时刻$ k $ , 都有下式成立:$$ M-\sum\limits_{j = 1}^Mp_{ij}[k]\leq f $$ 虽然本文考虑的是固定无向拓扑, 但在DoS攻击影响下, 可以看到系统的通信图却会与之发生变化. 因此, 本文接下去用时变图符号
${\cal G}[k] = ({\cal V},{\cal E}[k],\mathrm{A}[k])$ 表示系统在DoS攻击影响下的真实通信情况.假设2. 存在一个标量
$ \eta $ 满足$ 0<\eta<1 $ , 对于所有的$i,j\in\{1,\cdots,M\}$ , 如果$ a_{ij}[k]>0 $ , 那么$\eta\leq a_{ij}[k] < 1$ .假设3. 系统任意节点状态值
$x_i \in {\bf {R}}^N$ 受限于一个非空闭凸集, 表示为${\cal X}_i \in {\bf {R}}^N$ , 令$ {\cal X} = \cap_{i = 1}^M{\cal X}_i $ , 则$ {\cal X} \neq {\emptyset } $ .根据上述假设, 可以得出系统具备如下属性:
引理3[38]. 当系统的网络通信图为有向连通图且邻接矩阵为双随机矩阵时, 并且满足假设2和3时, 那么对于系统中任意节点
$ v_i \in {\cal V} $ 在动态更新式$ (1) $ 下, 有:$$ \lim\limits_{k\rightarrow\infty}\|x_i[k]-h[k]\| = 0 $$ (5) $$ \lim\limits_{k\rightarrow\infty}\|w_i[k]-h[k]\| = 0 $$ (6) 式中,
$ \{h[k]\} $ 为一个定义的辅助序列, 对于每个时刻$ k $ , 有:$$ h[k] = \frac{1}{M}\sum\limits_{i = 1}^Mw_i[k] $$ (7) $$ w_i[k] = \sum\limits_{j = 1}^Ma_{ij}[k]x_j[k] $$ (8) 根据文献[38], 因邻接矩阵为双随机矩阵, 由式(7) ~ (8)可得:
$$ \begin{split} h[k]=\;& \frac{1}{M}\sum\limits_{i = 1}^M\big(\sum\limits_{j = 1}^M a_{ij}[k]x_j[k]\big)=\\ & \frac{1}{M}\sum\limits_{j = 1}^Mx_j[k] \end{split} $$ (9) 将式(9)代入式(5), 即:
$$ \lim\limits_{k\rightarrow\infty}x_i[k] = \frac{1}{M}\sum\limits_{j = 1}^Mx_j[k] $$ (10) 引理4. 当系统的网络通信图为无向连通图, 并且满足假设2和3时, 那么由引理3可知, 对于系统中任意节点
$ v_i \in {\cal V} $ 在动态更新式(1)下, 式(10)仍然成立.证明. 根据引理3可知, 在网络通信图为有向图情况下, 邻接矩阵为双随机矩阵表明在该网络通信图中, 所有节点通信链路满足出度等于入度的条件, 而在无向图中, 该条件同样成立, 因此在无向图中, 式(10)仍然成立. □
针对上述建立的网络攻击模型和相关的系统假设, 本文的研究目标是, 设计一种控制策略, 使得: 1)系统的输出达到趋同并且趋同值是等于所有智能体初始输出状态的平均值; 2)在整个趋同过程中保护每个节点的信息值隐私.
3. 控制器设计
3.1 DoS攻击下网络拓扑鲁棒性条件
首先对网络通信链路图的鲁棒性条件进行讨论, 以便于开展后续控制器的设计工作.
引理5. 考虑多智能体系统(4), 如果其网络拓扑结构满足
$ (f+1) $ -鲁棒的无向图, 那么系统在遭受f-本地有界DoS攻击下, 即满足假设1, 其通信图仍可保持连通性.证明. 根据假设1可知, 网络中每个节点任意时刻至多有
$ f $ 条通信链路遭受DoS攻击破坏. 再由引理1可知, 此时网络拓扑结构至少是1-鲁棒图. 最后由引理2可知, 系统网络拓扑仍然能够保持连通性. □3.2 DoS攻击下隐私保护控制
上述小节给出了系统遭受DoS攻击下通信网络仍旧保持连通的条件, 接下去本小节给出本文核心的控制器设计方法.
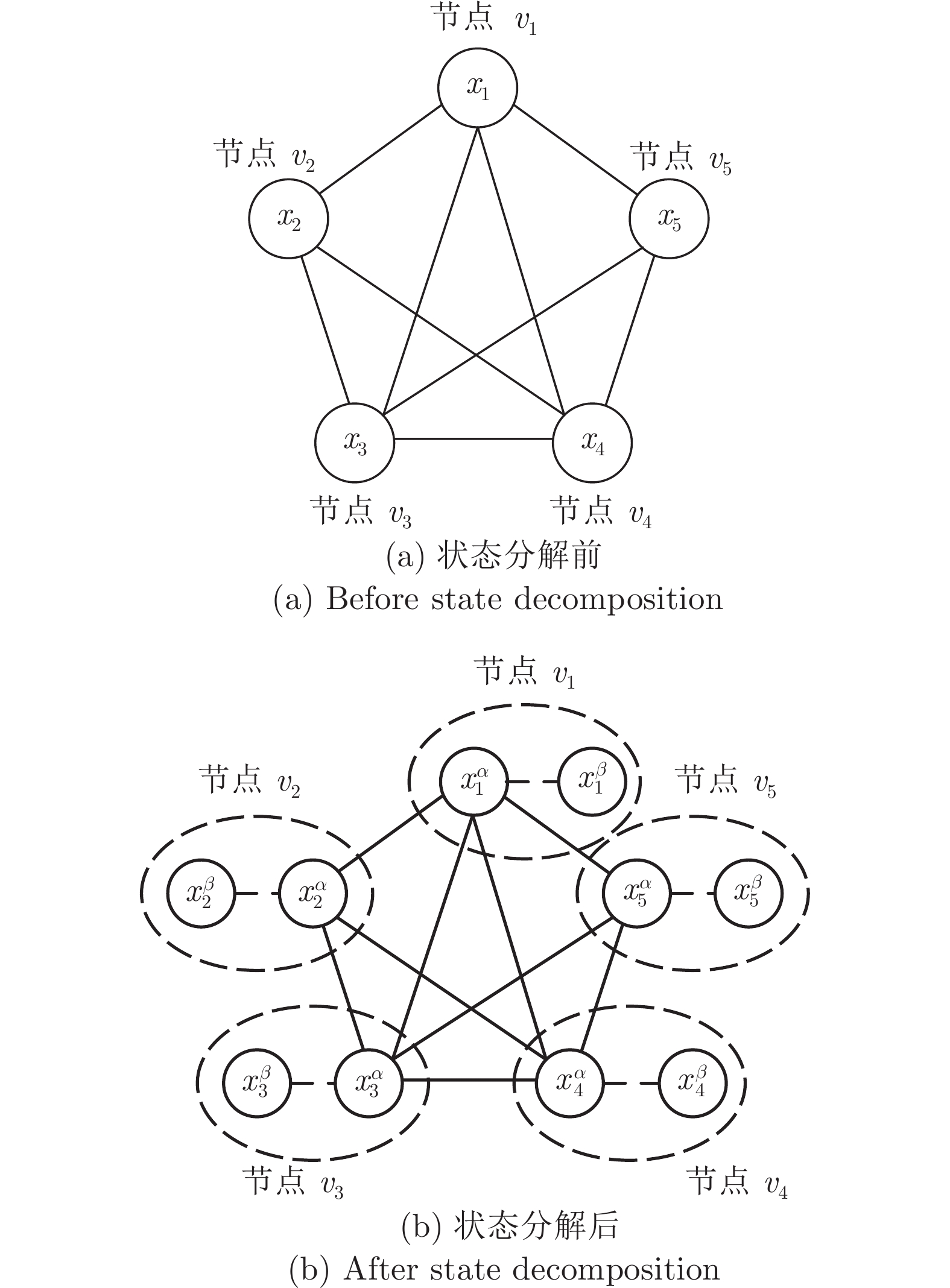
受文献[13]启发, 此处引入状态分解方法: 将每个节点的状态值
$ x_i $ 分解成两个子状态, 用$ x_i^{\alpha} $ 和$ x_i^{\beta} $ 表示. 值得注意的是, 初始状态的子状态值$ x_i^{\alpha}[0] $ 和$ x_i^{\beta}[0] $ 可在所有实数中任取, 但需满足条件:$ x_i^{\alpha}[0]+ x_i^{\beta}[0] = 2x_i[0] $ .为便于理解, 本文以5个节点的无向连通图为例, 通信拓扑如图2所示. 从示例图中可以看出: 子状态
$ x_i^{\alpha} $ 充当原$ x_i $ 的作用, 即与邻居节点进行信息交互, 并且实际上是节点$ v_i $ 的邻居节点唯一可以获知的状态信息. 而另一个子状态$ x_i^{\beta} $ 同样存在于该分布式信息交互中, 但是其仅与$ x_i^{\alpha} $ 进行信息交互. 也就是说子状态$ x_i^{\beta} $ 的存在, 对于节点$ v_i $ 的邻居节点是不可见的. 例如, 在图2(b)中, 节点$ v_1 $ 中的$ x_1^{\alpha} $ 相当于图2(a)中$ x_1 $ 的角色和邻居节点进行信息交互, 而$ x_1^{\beta} $ 仅对节点$ v_1 $ 自身可见, 而对其他节点不可见. 但是它又可以影响$ x_1^{\alpha} $ 的变化. 两个子状态$ x_i^{\alpha} $ 和$ x_i^{\beta} $ 之间的耦合权重是对称的, 表示为$ a_{i,\alpha\beta}[k] $ , 并且所有的$ a_{i,\alpha\beta}[k] $ 满足$ \eta\leq a_{i,\alpha\beta}[k]<1 $ .基于上述方法, 本文给出具体的具备隐私保护的输出均值趋同控制协议:
$$ \left\{ \begin{aligned}& x^\alpha[k+1] = P_\varepsilon[k]y[k]+\varepsilon A_{\alpha\beta}[k](x^\alpha[k]-x^\beta[k])\\ &x^\beta[k+1] = x^\beta[k]+\varepsilon A_{\alpha\beta}[k](x^\beta[k]-x^\alpha[k])\\ &y[k] = nCx^\alpha[k] \end{aligned} \right. $$ (11) 定义:
$$ x^\alpha[k] := \big[x_1^\alpha[k],\cdots,x_M^\alpha[k]\big]^{\rm{T}}\in{\bf {R}}^M $$ (12) $$ x^\beta[k]:= \big[x_1^\beta[k],\cdots,x_M^\beta[k]\big]^{\rm{T}}\in{\bf {R}}^M $$ (13) 并且
$$ P_\varepsilon[k]:= {\boldsymbol I}-\varepsilon{L}'[k] $$ (14) 式中,
$\boldsymbol I$ 为单位矩阵,${{\boldsymbol{L}}}'[k]$ 为DoS攻击下的Laplacian矩阵, 其满足:$$ {{\boldsymbol{L}}}'[k] = {{\boldsymbol{D}}}'[k]-{{\boldsymbol{A}}}'[k] $$ (15) 式中, DoS攻击下系统对应的邻接矩阵为
${{\boldsymbol{A}}}'[k] = \big[a_{ij}'[k]\big]$ , 满足:$$ a'_{ij}[k] = \left\{ \begin{aligned} &a_{ij}[k],& k<k_0\\ &a_{ij}[k]p_{ij}[k], &k\geq k_0 \end{aligned} \right. $$ (16) ${{\boldsymbol{D}}}'[k]$ 为对应于邻接矩阵${A}'[k]$ 的度矩阵.另外, 在协议(11)中,
$y[k] = n{C}x^\alpha[k]$ 为系统的状态输出方程,${{\boldsymbol{C}}}$ 为输出方程的观测矩阵, 定义为:$$ {{\boldsymbol{C}}}:= [{\boldsymbol {e}}_1,\;\cdots,\; {\boldsymbol {e}}_{M-1},\; {\boldsymbol {e}}_M]^{\rm T}\in{\bf {R}}^{M\times M} $$ (17) 式中,
${\boldsymbol {e}}_i$ 表示${\bf {R}}^M$ 中第$ i $ 个规范基向量, 该向量中第$ i $ 个位置数为1, 其他位置数为0.注1. 考虑实际环境中不同情况, 当
$ n\in(0,1) $ 时, 系统输出方程将会缩小状态值进行信息交互, 适用于节点状态值过大的情况; 当$ n = 1 $ 时, 系统状态输出方程将会输出原本节点需要进行信息交互的状态值; 当$ n\in(1,\infty) $ 时, 系统状态输出方程将会放大状态值进行信息交互, 适用于节点状态值过小的情况.值得注意的是, 对于系统中的节点, 用于和邻居节点进行信息交互的状态值
$ x^\alpha[k] $ 是无法被邻居节点获取的, 需通过系统状态输出方程传递给邻居节点. 简言之每个节点经过信息交互接收到的邻居节点的值并不是$ x^\alpha[k] $ , 而是经过输出方程输出的$ y[k] $ .令
${{\boldsymbol{A}}}_{\alpha\beta}[k]$ 为每个节点$v_i, i = 1,2,\cdots, M$ 的$ x_i^\alpha[k] $ 和$ x_i^\beta[k] $ 两个子状态之间的耦合权重$ a_{i,\alpha\beta}[k] $ 对应的矩阵, 定义为$$ {{\boldsymbol{A}}}_{\alpha\beta}[k]:= [a_{1,\alpha\beta}[k],\cdots,a_{M,\alpha\beta}[k]]\in{\bf {R}}^M $$ (18) 为便于叙述, 本文考虑节点的状态值及输出值为一维的情况, 即令
$ N = 1, Q = 1 $ . 从而, 基于输出状态值的控制协议可表示为:$$ \left\{ \begin{aligned} &x_i^\alpha[k+1] = x_i^\alpha[k]+\varepsilon\sum\limits_{j = 1}^Ma'_{ij}[k](y_j[k]-y_i[k])+\\ & \qquad\qquad\quad\;\;\varepsilon a_{i,\alpha\beta}[k](x_i^\beta[k]-x_i^\alpha[k])\\ &x_i^\beta[k+1] = x_i^\beta[k]+\varepsilon a_{i,\alpha\beta}[k](x_i^\alpha[k]-x_i^\beta[k])\\ &y_i[k]= nx_i^\alpha[k] \end{aligned} \right. $$ (19) 事实上, 只要向量状态中的每个标量状态元素都有独立的耦合权重, 本节所提出的控制方法所有分析及结果同样适用于向量状态的情况.
注2. 与文献[13, 37]的更新式(1)相比, 本文给出的协议(19)中, 由于每个可见子状态的邻居数增加了一个
$ ( $ 不可见子状态$ ) $ , 因此$ \varepsilon $ 的上限从${1}/{\Delta}$ 降低为${1}/{(\Delta+1)}$ .注3. 相比于文献[13, 37]设计的更新式(1), 本文在协议(19)的设计过程中考虑了系统通信链路中存在DoS攻击的情况, 可确保在存在一定能力DoS攻击时, 系统在协议(19)的约束下实现均值趋同.
3.3 输出均值趋同分析
在给出本文主要结论前, 需要下述引理知识.
引理6. 考虑多智能体系统(4), 如果其网络通信图是一个无向连通图, 则对于状态分解后的网络, 所有节点子状态总和是固定不变的.
证明. 由输出方程
$ y_i[k] = nx_i^\alpha[k] $ , 推导可得:$$ y_i[k+1] = nx_i^\alpha[k+1] $$ (20) 再将式(20)代入式(19), 可得:
$$ \left\{ \begin{aligned} &\frac{1}{n}y_i[k+1] = x_i^\alpha[k+1]=x_i^\alpha[k]+\\ & \qquad\qquad\quad\;\; \varepsilon\sum\limits_{j = 1}^Ma'_{ij}[k](y_j[k]-y_i[k])+\\ &\qquad\qquad\quad\;\;\varepsilon a_{i,\alpha\beta}[k](x_i^\beta[k]-x_i^\alpha[k])\\ &x_i^\beta[k+1] = x_i^\beta[k]+\varepsilon a_{i,\alpha\beta}[k](x_i^\alpha[k]-x_i^\beta[k]) \end{aligned} \right. $$ (21) 进一步, 由式(21), 可得:
$$ \begin{split} &x_i^\alpha[k+1]+x_i^\beta[k+1]=x_i^\alpha[k]+\\ & \quad x_i^\beta[k]+\varepsilon\sum\limits_{j = 1}^Ma'_{ij}[k](y_j[k]-y_i[k])+\\ &\quad\varepsilon a_{i,\alpha\beta}[k](x_i^\beta[k]-x_i^\alpha[k])+\\ &\quad \varepsilon a_{i,\alpha\beta}[k](x_i^\alpha[k]-x_i^\beta[k])=\\ & \quad x_i^\alpha[k]+x_i^\beta[k]+\varepsilon\sum\limits_{j = 1}^Ma'_{ij}[k](y_j[k]-y_i[k])\\[-15pt] \end{split} $$ (22) 因此有:
$$ \begin{split} &\sum\limits_{i = 1}^M(x_i^\alpha[k+1]+x_i^\beta[k+1])= \sum\limits_{i = 1}^M(x_i^\alpha[k]+x_i^\beta[k])+\\ &\quad\varepsilon\sum\limits_{i = 1}^{M}\left\{\sum\limits_{j = 1}^Ma'_{ij}[k]\big(y_j[k]-y_i[k]\big)\right\}\\[-20pt] \end{split} $$ (23) 而在式(23)中的
$\sum\nolimits_{i = 1}^{M}\Big\{\sum\nolimits_{j = 1}^Ma'_{ij}[k]\big(y_j[k]- y_i[k]\big)\Big\}$ 部分, 可进一步分解为下式:$$ \begin{split} &\sum\limits_{i = 1}^{M}\left\{\sum\limits_{j = 1}^Ma'_{ij}[k]\big(y_j[k]-y_i[k]\big)\right\}=\\ &\quad \sum\limits_{i = 1}^M\{a'_{i1}[k](y_1[k]-y_i[k])+a'_{i2}[k](y_2[k]-\\ &\quad y_i[k])+\ldots+a'_{iM}[k](y_M[k]-y_i[k])\}=\\ &\quad a'_{11}[k](y_1[k]-y_1[k])+a'_{12}[k](y_2[k]-y_1[k])+\cdots+\\ &\quad a'_{1M}[k](y_M[k]-y_1[k])+\\ &\quad a'_{21}[k](y_1[k]-y_2[k])+a'_{22}[k](y_2[k]-y_2[k])+\cdots+\\ &\quad a'_{2M}[k](y_M[k]-y_2[k])+\\ &\quad a'_{31}[k](y_1[k]-y_3[k])+a'_{32}[k](y_2[k]-y_3[k])+\cdots+\\ &\quad a'_{3M}[k](y_M[k]-y_3[k])+ \\ &\qquad \quad\vdots\\ &\quad a'_{M1}[k](y_1[k]-y_M[k])+a'_{M2}[k](y_2[k]-\\ &\quad y_M[k])+\cdots+a'_{MM}[k](y_M[k]-y_M[k])\\[-10pt] \end{split} $$ (24) 根据无向图属性:
$a'_{ij}[k] = a'_{ji}[k]$ , 对于任意$v_i, v_j \in {\cal V}$ , 有:$$ a'_{ij}[k](y_j[k]-y_i[k]) = -a'_{ji}[k](y_i[k]-y_j[k]) $$ (25) 将式(25)代入式(24), 可得:
$$ \sum\limits_{i = 1}^{M}\left\{\sum\limits_{j = 1}^Ma'_{ij}[k]\big(y_j[k]-y_i[k]\big)\right\} = 0 $$ (26) 将式
$ (26) $ 代入式$ (23) $ , 可得:$$ \sum\limits_{i = 1}^M(x_i^\alpha[k+1]+x_i^\beta[k+1]) = \sum\limits_{i = 1}^M(x_i^\alpha[k]+x_i^\beta[k]) $$ (27) 由式(27)容易看出, 对于进行状态分解后的网络, 系统节点子状态的和是固定不变的. □
下面给出本文的主要结论.
定理1. 考虑DoS攻击下多智能体系统(4), 在满足假设1、2和3条件下, 若其通信拓扑满足
$(f+ 1)$ -鲁棒图, 且系统节点在所给的分布式协议(19)下进行状态更新, 则系统可实现输出值均值趋同.证明. 由于系统的通信图是一个
$ (f+1) $ -鲁棒图, 根据引理5可知, 系统在满足假设1的DoS攻击下, 其网络图仍能够保持连通. 显然, 经过状态分解之后的系统同样能够保证网络图的连通性. 根据引理6, 当$ k = 0 $ 时, 有:$$ \frac{1}{2M}\sum\limits_{i = 1}^M(x_i^\alpha[1]+x_i^\beta[1]) = \frac{1}{2M}\sum\limits_{i = 1}^M(x_i^\alpha[0]+x_i^\beta[0]) $$ (28) 随后, 根据引理4和式(28)可知, 系统可以实现均值趋同, 即任意节点的子状态
$ x_i^\alpha[k] $ 和$ x_i^\beta[k] $ 都将收敛至:$$ \frac{1}{2M}\sum\limits_{i = 1}^M(x_i^\alpha[1]+x_i^\beta[1]) $$ 再根据式(28)和状态分解约束条件
$x_i^\alpha[0]+ x_i^\beta[0] = 2x_i[0]$ , 可得:$$ \lim\limits_{k\rightarrow\infty}x_i^\alpha[k] = \lim\limits_{k\rightarrow\infty}x_i^\beta[k] = \frac{1}{M}\sum\limits_{j = 1}^Mx_j[0] $$ (29) 最后, 根据式(29)和输出方程
$ y_i[k] = nx_i^\alpha[k] $ , 可得:$$ \lim\limits_{k\rightarrow\infty}y_i[k] = \lim\limits_{k\rightarrow\infty}nx_i^\alpha[k] = \frac{n}{M}\sum\limits_{j = 1}^Mx_j[0] $$ (30) □
注4. 相比于文献[13]设计的隐私保护状态更新协议, 本文在协议(19)的设计过程中进一步考虑了在实际环境对测量条件等的限制导致难以获得系统中节点的真实状态值的情况, 引入了节点输出值的概念, 通过观测矩阵获取的系统输出
$ y $ 进行协议(19)的设计, 可确保系统在该协议下实现输出值均值趋同.3.4 隐私保护分析
本节对趋同控制过程中单个节点信息的隐私保护进行分析. 本文考虑两种隐私窃听者: 好奇窃听者和外部窃听者. 好奇窃听者是指一类能够正确遵循所有控制协议步骤但具有好奇性的节点, 这类节点会收集接收到的数据并试图猜测其他节点的状态信息. 而外部窃听者是指一类了解整个网络拓扑结构的外部节点, 并能够窃听某些内部节点的通信链路从而获得在该通信链路交互的信息.
一般来说, 这里的外部窃听者比好奇窃听者更具有破坏力, 因为外部窃听者会窃听多个节点通信链路上交互的信息, 而好奇窃听者只能窃听该节点通信链路交互的信息, 但好奇窃听者有一个外部窃听者无法得知的信息, 即该好奇窃听者的初始状态值.
定义好奇窃听者
$ v_i \in {\cal V} $ 在第$ k $ 次迭代时所获得的信息为:$I_i[k] = \{a'_{ip}[k]|_{{v_p}\in {{\cal N}}_i},y_p[k]|_{{v_p}\in {{\cal N}}_i},x_i[k],$ $x_i^\alpha[k], x_i^\beta[k],a_{i,\alpha\beta}[k]\}$ . 随着状态值迭代更新, 窃听者$ v_i $ 收集获得的信息表示为$ I_i = \bigcup\nolimits_{k = 0}^{\infty}I_i[k] $ .定义4. 如果窃听者无法以任何精度保证估计节点状态信息
$ x_i[0] $ 的值, 则称节点$ v_i $ 得到了隐私保护.在给出结论前, 需要用到下述引理.
引理7[13]. 在采用状态分解方法的信息交互通信中, 如果正常节点
$ v_j $ 具有至少一个不与好奇窃听节点$ v_i $ 直接相连的正常邻居节点$ v_m $ , 则对于节点$ v_j $ 的任意初始状态$ \overline{x}_j[0]\neq x_j[0] $ , 窃听节点$ v_i $ 获得的信息始终满足$ \overline{I}_i = I_i $ .引理8[13]. 在采用状态分解方法的信息交互通信中, 如果正常节点
$ v_j $ 存在至少一个正常邻居节点$ v_m $ , 其$ a_{jm}[0] $ 的值对于外部窃听者不可见, 则节点$ v_j $ 的任意初始状态的任何变化都可以完全通过对外部窃听者不可见的$ a_{jm}[0] $ ,$ a_{j,\alpha\beta}[0] $ 和$ a_{m,\alpha\beta}[0] $ 的变化来补偿, 因此外部窃听者无法以任何精度保证估计正常节点$ v_j $ 的初始状态值$ x_j[0] $ .定理2. 考虑DoS攻击下多智能体系统(4), 对于系统中任意正常节点
$ v_j \in {\cal V} $ , 如果$ v_j $ 在所给的分布式协议(19)下进行状态更新, 则在整个信息交互过程中, 其状态信息值$ x_j[0] $ 具备隐私保护.证明. 首先, 分析系统存在好奇窃听者
$ v_i $ 的情况. 对于任意正常节点$ v_j $ , 在所给的分布式协议(19)下, 其初始状态显然满足$ \overline{x}_j[0]\neq x_j[0] $ ,$ \overline{I}_i = I_i $ . 再由引理6可知, 该条件下好奇窃听者无法准确估计节点$ v_j $ 的初始值, 因此节点$ v_j $ 的状态值$ x_j[0] $ 得到了隐私保护.随后, 分析系统存在外部窃听者的情况. 在本文所提的分布式算法(19)下, 外部窃听者对于系统中任意正常节点
$ v_j \in {\cal V} $ 的其中之一子状态不可见. 根据引理7,$ v_j $ 初始状态值的变化则对于外部窃听者不可见, 故外部窃听者无法准确估计正常节点$ v_j $ 的初始值, 因此节点$ v_j $ 的状态值$ x_j[0] $ 得到了隐私保护. □4. 数值仿真
本节通过一些仿真算例来验证提出算法的有效性. 同时与文献[13]中的算法进行了比较, 以验证其优势.
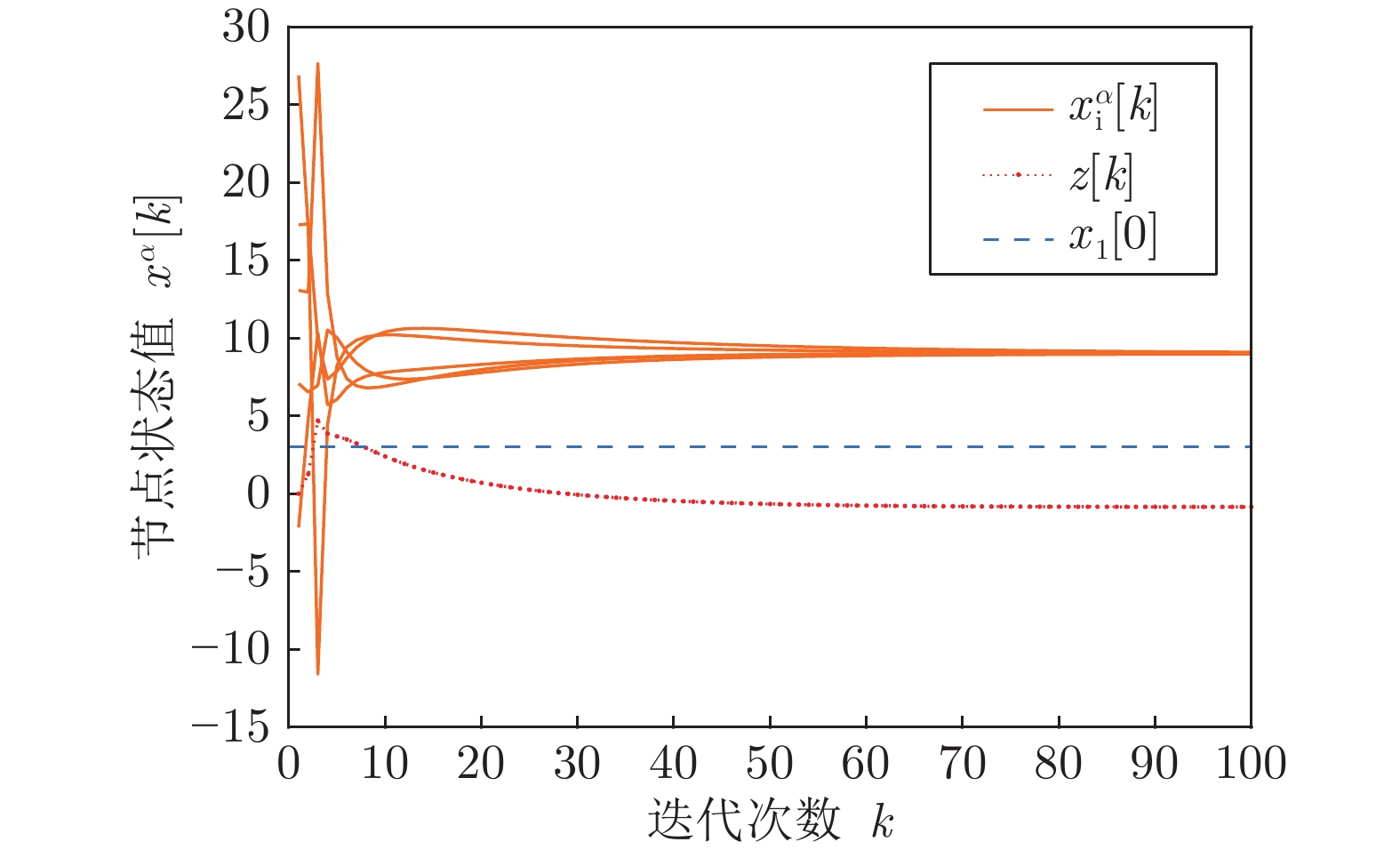
考虑由5个节点组成的无向图网络, 其通信拓扑如图3所示. 每个节点分别赋予初始状态值
$x_1[0] = 3$ ,$ x_2[0] = 6 $ ,$ x_3[0] = 9 $ ,$ x_4[0] = 12 $ ,$ x_5[0] = 15 $ .首先考虑节点采用文献[13]中的控制律更新状态, 令
$ \varepsilon = 0.2 $ , 对应的邻接矩阵设置为:$$ {\boldsymbol{{A}}}_1 = 0.75\left[ \begin{aligned} 0\;\;\;&1&0\;\;\;&0&1\\ 1\;\;\;&0&1\;\;\;&0&0\\ 0\;\;\;&1&0\;\;\;&0&1\\ 0\;\;\;&0&0\;\;\;&0&1\\ 1\;\;\;&0&1\;\;\;&1&0 \end{aligned}\right] $$ (31) 值得注意的是, 文献[13]并未涉及输出方程, 因此不妨用
$ x_i $ 表示节点$ v_i $ 的内部状态,$ x_i^+ $ 表示和邻居节点进行交互的状态值.考虑存在外部窃听者试图猜测节点
$ v_1 $ 的初始状态值$ x_1[0] $ . 可以构造以下的外部窃听者对节点$ v_1 $ 的初始状态值进行估计:$$ \begin{split} &z[k+1] =z[k]+x_1^+[k+1]-\\ &\quad\left(x_1^+[k]+\varepsilon\sum\limits_{j = 1}^Ma_{1j}(x_j^+[k]-x_1^+[k])\right) \end{split} $$ (32) 式中,
$ z[k] $ 表示窃听者在$ k $ 时刻获知的观测状态. 显然, 外部窃听者初始观测状态$ z[0] = x_1^+[0] $ . 假设该外部窃听者除了不可获知节点$ v_1 $ 与$ v_2 $ 之间的权值$ a_{12}[0] $ 外, 具备整个网络其他的拓扑信息. 此时给$ a_{12}[0] $ 随机赋值0.7.系统中各个节点的状态变化轨迹如图4所示. 图中实线表示各节点
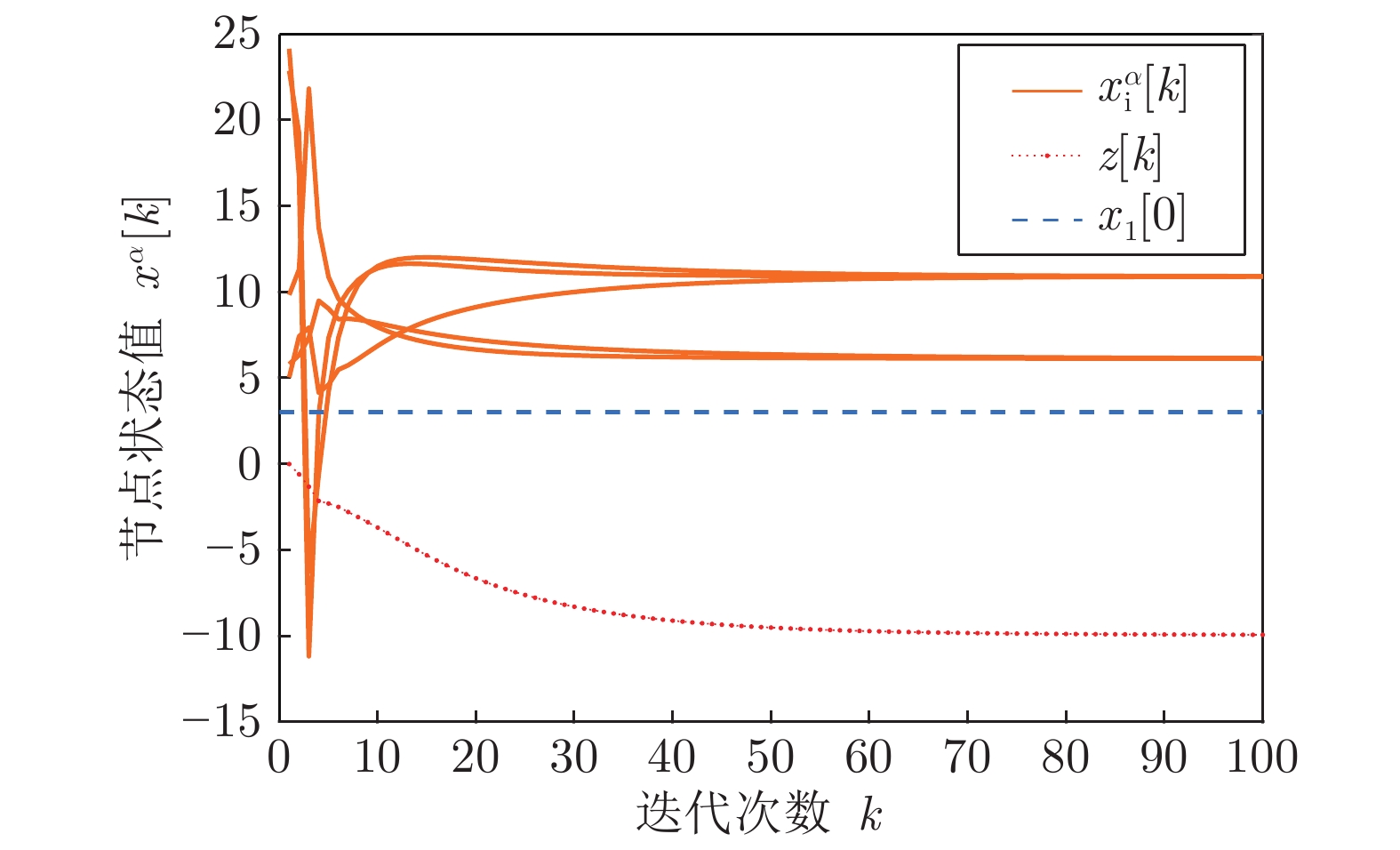
$ \alpha $ 子状态值变化曲线, 点连线表示外部窃听者对节点$ v_1 $ 初始状态值的猜测曲线, 虚线表示节点$ v_1 $ 的初始状态值. 可以看出, 在无DoS攻击影响下, 文献[13]中的控制方法可使系统准确收敛到所有节点初始状态的均值9, 且外部窃听者不能准确推断节点$ v_1 $ 的初始状态$ x_1[0] = 3 $ .然后, 考虑网络中存在DoS攻击的情况. 不妨令
$ f = 2 $ , 相应的, Adversory$({P},k_0)$ 中的攻击矩阵为:$$ {\boldsymbol P } = \begin{bmatrix} 1&0&1&1&1\\ 0&1&1&1&1\\ 1&1&1&1&0\\ 1&1&1&1&1\\ 1&1&0&1&1 \end{bmatrix} $$ (33) 令
$ k_0 = 5 $ , 即表示系统在第5次状态更新时, 开始发生DoS攻击, 并且持续发生至更新结束.图5显示的是在上述攻击影响下基于文献[13]中算法的系统各个节点的状态变化曲线. 图5中实线表示各节点
$ \alpha $ 子状态值变化曲线, 点连线表示外部窃听者对节点$ v_1 $ 初始状态值的猜测曲线, 虚线表示节点$ v_1 $ 的初始状态值. 从中可以明显看到, 在DoS攻击下, 尽管系统仍具备保护隐私的能力, 但系统中各个节点的状态则无法达成趋同.考虑遭受同样满足Adversory
$({P},k_0)$ 的DoS攻击, 重新设计网络拓扑结构, 使其满足定理1中的通信图要求, 即满足3-鲁棒图. 设计后的网络通信图如图6所示.同样令
$ \varepsilon = 0.2 $ , 邻接矩阵设置为:$$ {\boldsymbol A }_2 = 0.75 \begin{bmatrix} 0&1&1&1&1\\ 1&0&1&1&0\\ 1&1&0&1&1\\ 1&1&1&0&1\\ 1&0&1&1&0 \end{bmatrix} $$ (34) 同样考虑存在一个外部窃听者试图猜测节点
$ v_1 $ 的初始状态值. 考虑此时传输的是输出状态, 令$ y_i $ 表示节点$ v_i $ 和邻居节点进行交互的信息值, 输出方程中观测矩阵前系数$ n = 1 $ , 构造以下的外部窃听者对节点$ v_1 $ 的初始状态值进行猜测:$$ \begin{split} &z[k+1] = z[k]+y_1[k+1]-\\ &\quad \left(y_1[k]+\varepsilon\sum\limits_{j = 1}^Ma_{1j}(y_j[k]-y_1[k])\right) \end{split} $$ (35) 外部窃听者初始观测状态
$ z[0] = y_1[0] $ . 根据定理2中的条件, 实例中假设外部窃听者可以获得除了节点$ v_1 $ 和$ v_2 $ 之间的权值$ a_{12}[0] $ 外的整个拓扑图信息. 同样为$ a_{12}[0] $ 随机赋值0.7. 因此, 根据定理1和定理2可知, 系统节点在满足图6所给的通信图下, 在本文控制协议下可以达成均值趋同, 且每个节点的状态信息得到隐私保护.图7显示的是在DoS攻击下系统节点在本文所提控制方法下的状态变化轨迹. 其中实线表示各节点输出值变化曲线, 点连线表示外部窃听者对节点
$ v_1 $ 初始状态值的猜测曲线, 虚线表示节点$ v_1 $ 的初始状态值. 由图7可以看出, 系统在DoS攻击下仍然可以收敛到所有节点初始输出状态的平均值9, 且外部窃听者无法成功估计节点$ v_1 $ 的初始值. 仿真结果验证了本文方法的有效性.5. 结束语
本文针对DoS攻击下无向多智能体网络趋同问题, 提出了一种具有节点信息隐私保护能力的趋同方法, 实现了DoS攻击下系统输出值的均值趋同. 结合状态分解方法, 设计了节点输出状态的初始值隐私保护策略, 保证所有节点信息在分布式算法邻居间信息交互过程中不被窃听者窃取. 进一步, 借助r-鲁棒图概念, 分析给出了系统在所建立DoS攻击模型下的通信网络拓扑要求, 并设计了相应的输出均值趋同控制协议. 最后, 通过一组数值仿真实验验证了所提方法的有效性.
同时, 本文目前研究设计的输出均值趋同控制协议还存在着一定的不足值得在进一步的研究中进行改进. 1)该输出均值趋同协议目前仅适用于无向拓扑网络, 而在现实生活中, 有向图更加普遍, 因此接下来的研究将致力于针对有向拓扑情况, 对本文所设计的输出均值趋同控制协议进行进一步的改进. 2)本文为了抵御系统所遭受的DoS攻击, 通过增加通信链路来增强网络拓扑的连通性, 这一定程度上增加了通信的成本, 因此寻找一个能够解决通信成本大幅度增加的问题的方法是接下来值得研究的方向.
-
[1] 李韬, 孟杨, 张纪峰. 多自主体量化趋同与有限数据率趋同综述. 自动化学报, 2013, 39(11): 1805−1811 doi: 10.3724/SP.J.1004.2013.01805Li Tao, Meng Yang, Zhang Ji-Feng. An overview on quantized consensus and consensus with limited data rate of multi-agent systems. Acta Automatica Sinica, 2013, 39(11): 1805−1811 doi: 10.3724/SP.J.1004.2013.01805 [2] 杨洪勇, 郭雷, 张玉玲, 姚秀明. 离散时间分数阶多自主体系统的时延一致性. 自动化学报, 2014, 40(9): 2022−2028Yang Hong-Yong, Guo Lei, Zhang Yu-Ling, Yao Xiu-Ming. Delay consensus of fractional-order multi-agent systems with sampling delays. Acta Automatica Sinica, 2014, 40(9): 2022−2028 [3] Yao A C. Protocols for secure computations. In: Proceedings of the 23rd Annual Symposium on Foundations of Computer Science. Chicago, IL, USA: IEEE, 1982. 160−164 [4] Shamir A, How to share a secret. Communication of the ACM, 1979, 22: 612−613 doi: 10.1145/359168.359176 [5] Kreuter B, Shelat A, Shen C H. Billion-gate secure computation with malicious adversaries. In: Proceedings of the 21st USENIX Conference on Security Symposium. Berkeley, USA: USENIX Association, 2012. 285−300 [6] Chen W, Cai S. Ad hoc peer-to-peer network architecture for vehicle safety communications. IEEE Communications Magazine, 2005, 43(4): 100−107 doi: 10.1109/MCOM.2005.1421912 [7] Huang Z, Mitra S, Vaidya N. Differentially private distributed optimization. In: Proceedings of the 2015 International Conference on Distributed Computing and Networking. NewYork, USA: ACM, 2015. 1−10 [8] Nozari E, Tallapragada P, Cortes J. Differentially private average consensus: obstructions, trade-offs, and optimal algorithm design. Automatica, 2017, 81(7): 221−231 [9] Katewa V, Pasqualetti F, Gupta V. On privacy vs cooperation in multi-agent systems. International Journal of Control, 2018, 91(7): 1693−1707 doi: 10.1080/00207179.2017.1326632 [10] Huang Z, Mitra S, Dullerud G. Differentially private iterative synchronous consensus. In: Proceedings of the 2012 ACM Workshop on Privacy in The Electronic Society. NewYork, USA: ACM, 2012. 81−90 [11] Nozari E, Tallapragada P, Cortes J. Differentially private average consensus with optimal noise selection. IFAC-PapersOnline, 2015, 48(22): 203−205 doi: 10.1016/j.ifacol.2015.10.331 [12] Manitara N, Hadjicostis C. Privacy-preserving asymptotic average consensus. In: Proceedings of the 2013 European Control Conference (ECC). Zurich, Switzerland: IEEE, 2013. 760−765 [13] Wang Y. Privacy-preserving average consensus via state decomposition. IEEE Transactions on Automatic Control, 2019, 64(11): 4711−4716 doi: 10.1109/TAC.2019.2902731 [14] Kia S, Cortes J, Martinez S. Dynamic average consensus under limited control authority and privacy requirements. International Journal of Robust and Nonlinear Control, 2015, 25(13): 1941−1966 doi: 10.1002/rnc.3178 [15] Pequito S, Kar S, Sundaram S, Aguiar A P. Design of communication networks for distributed computation with privacy guarantees. In: Proceedings of the 2015 54th IEEE Conference on Decision and Control (CDC). Osaka, Japan: IEEE, 2015. 1370−1376 [16] Alaeddini A, Morgansen K, Mesbahi M. Adaptive communication networks with privacy guarantees. In: Proceedings of the 2017 American Control Conference (ACC). Seattle, USA: IEEE, 2017. 4460−4465 [17] Gupta N, Chopra N. Confidentiality in distributed average information consensus. In: Proceedings of the 2016 IEEE 55th Conference on Decision and Control (CDC). Las Vegas, USA: IEEE, 2016. 6709−6714 [18] Kogiso K, Fujita T. Cyber-security enhancement of networked control systems using homomorphic encryption. In: Proceedings of the 2015 54th IEEE Conference on Decision and Control (CDC). Osaka, Japan: IEEE, 2015. 6836−6843 [19] Shoukry Y, Gatsis K, Alanwar A, Pappas G J, Seshia S A, Srivastava M, et al. Privacy-aware quadratic optimization using partially homomorphic encryption. In: Proceedings of the 2016 IEEE 55th Conference on Decision and Control (CDC). Las Vegas, USA: IEEE, 2016. 5053−5058 [20] Lagendijk R L, Erkin Z, Barni M. Encrypted signal processing for privacy protection: Conveying the utility of homomorphic encryption and multiparty computation. IEEE Signal Processing Magazine, 2013, 30(1): 82−105 doi: 10.1109/MSP.2012.2219653 [21] Zhang C, Ahmad M, Wang Y. Admm based privacy-preserving decentralized optimization. IEEE Transactions on Information Forensics and Security, 2019, 14(3): 565−580 doi: 10.1109/TIFS.2018.2855169 [22] LeBlanc H J, Zhang H, Koutsoukos X, Sundaram S. Resilient asymptotic consensus in robust networks. IEEE Journal on Selected Areas in Communications, 2013, 31(4): 766−781 doi: 10.1109/JSAC.2013.130413 [23] Wu Y, He X. Secure consensus control for multiagent systems with attacks and communication delays. IEEE/CAA Journal of Automatica Sinica, 2017, 4(1): 136−142 doi: 10.1109/JAS.2016.7510010 [24] Fiore D, Russo G. Resilient consensus for multi-agent systems subject to differential privacy requirements. Automatica, 2019, 106: 18−26 doi: 10.1016/j.automatica.2019.04.029 [25] 黄锦波, 伍益明, 何熊熊, 常丽萍. 信任节点机制下的异构多智能体系统安全一致性控制. 中国科学: 信息科学, 2019, 49(5): 599−612 doi: 10.1360/N112018-00343Huang Jin-Bo, Wu Yi-Ming, He Xiong-Xiong, Chang Li-Ping. Secure consensus control for heterogeneous multi-agent systems with trusted nodes. Sci Sin Inform, 2019, 49(5): 599−612 doi: 10.1360/N112018-00343 [26] Usevitch J, Panagou D. Resilient leaderfollower consensus to arbitrary reference values in time-varying graphs. IEEE Transactions on Automatic Control, 2020, 65(4): 1755−1762 doi: 10.1109/TAC.2019.2934954 [27] He W, Mo Z, Han Q L, Qian F. Secure impulsive synchronization in lipschitztype multi-agent systems subject to deception attacks. IEEE/CAA Journal of Automatica Sinica, 2020, 5(7): 1326−1334 [28] Fu W, Qin J, Shi Y, Zheng W X, Kang Y. Resilient consensus of discrete-time complex cyber-physical networks under deception attacks. IEEE Transactions on Industrial Informatics, 2020, 16(7): 4868−4877 doi: 10.1109/TII.2019.2933596 [29] Zhang D, Liu L, Feng G. Consensus of heterogeneous linear multiagent systems subject to aperiodic sampled-data and dos attack. IEEE Transactions on Cybernetics, 2019, 49(4): 1501−1511 doi: 10.1109/TCYB.2018.2806387 [30] Feng Z, Hu G. Secure cooperative event-triggered control of linear multiagent systems under dos attacks. IEEE Transactions on Control Systems Technology, 2020, 28(3): 741−752 doi: 10.1109/TCST.2019.2892032 [31] Yang Y, Xu H, Yue D. Observer-based distributed secure consensus control of a class of linear multi-agent systems subject to random attacks. IEEE Transactions on Circuits and Systems I: Regular Papers, 2019, 66(8): 3089−3099 doi: 10.1109/TCSI.2019.2904747 [32] Xu W, Hu G, Ho D W, Feng Z. Distributed secure cooperative control under denial-of-service attacks from multiple adversaries. IEEE Transactions on Cybernetics, 2020, 50(8): 3458−3467 doi: 10.1109/TCYB.2019.2896160 [33] Wen G, Wang P, Huang T, Lü J, Zhang F. Distributed Consensus of Layered Multi-Agent Systems Subject to Attacks on Edges. IEEE Transactions on Circuits and Systems I: Regular Papers, 2020, 67(9): 3152−3162 doi: 10.1109/TCSI.2020.2986953 [34] Zhang H, Fata E, Sundaram S. A notion of robustness in complex networks. IEEE Transactions on Control of Network Systems, 2015, 2(3): 310−320 doi: 10.1109/TCNS.2015.2413551 [35] Yin X, Tan C, Huang J. Output consensus for networks of heterogeneous linear agents. In: Proceedings of the 2017 36th Chinese Control Conference (CCC). Dalian, China: IEEE, 2017. 7679−7683 [36] Zhang H, Sundaram S. Robustness of information diffusion algorithms to locally bounded adversaries. In: Proceedings of the 2012 American Control Conference (ACC). Montréal, Canada: IEEE, 2012. 5855−5861 [37] Olfati-Saber R, Fax J A, Murray R M. Consensus and cooperation in networked multi-agent systems. Proceedings of the IEEE, 2007, 95(1): 215−233 doi: 10.1109/JPROC.2006.887293 [38] Nedic A, Ozdaglar A, Parrilo P A. Constrained consensus and optimization in multi-agent networks. IEEE Transactions on Automatic Control, 2010, 55(4): 922−938 doi: 10.1109/TAC.2010.2041686 [39] Yang Y, Li Y, Yue D, Tian Y, Ding X. Distributed secure consensus control with event-triggering for multiagent systems under dos attacks. IEEE Transactions on Cybernetics, DOI: 10.1109/TCYB.2020.2979342. 期刊类型引用(1)
1. 王元茂,欧阳婷. 移动社交网络用户的浏览隐私保护. 新乡学院学报. 2024(03): 39-43 .  百度学术
百度学术其他类型引用(8)
-































































 下载:
下载: